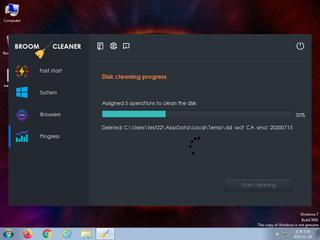
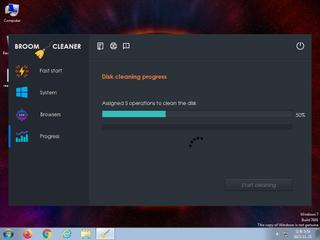
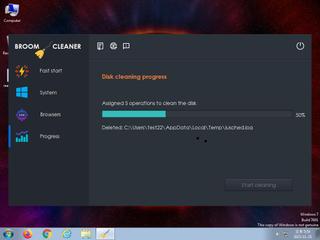
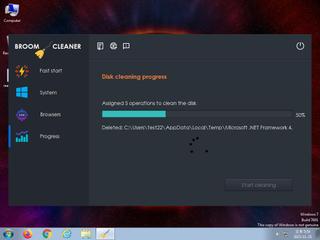
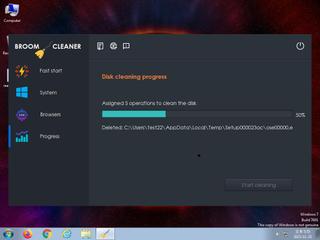
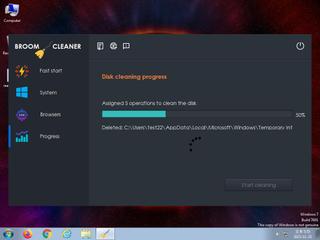
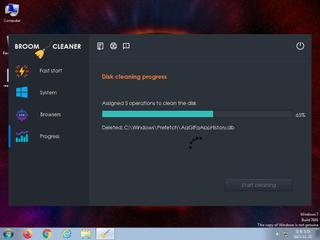
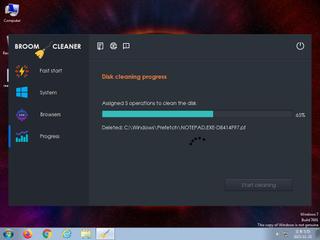
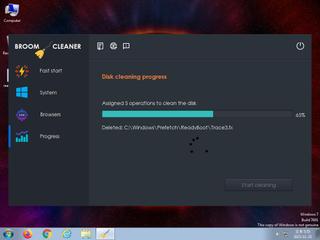
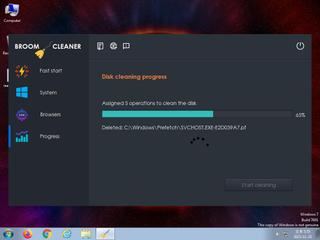
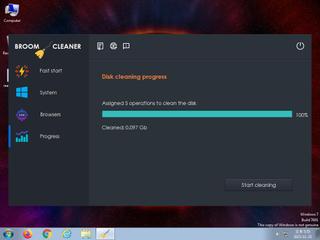
ScreenShot
| Created | 2023.11.25 17:58 | Machine | s1_win7_x6403 |
| Filename | decord.exe | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 54 detected (Common, ShortLoader, MSILZilla, GenericRXOO, unsafe, Save, Ransomware, Mokes, malicious, Attribute, HighConfidence, high confidence, keepis, DropperX, Anhl, ILAgent, AGEN, MulDropNET, SMOKELOADER, YXDKYZ, high, score, Static AI, Malicious PE, Detected, Kryptik, Eldorado, Glupteba, PHU5HG, ai score=82, GdSda, AntiVM, CLASSIC, Outbreak, susgen, GenKryptik, FFMZ, ZemsilF, @p0@aSkQmsk, confidence, 100%) | ||
| md5 | faa78f58b4f091f8c56ea622d8576703 | ||
| sha256 | 464c7ab944886103d617e334c94320344761a543de5395c6b541ae386b448ea0 | ||
| ssdeep | 196608:AR4ERFw+DIaY5cI1CmjxOSdKk7lpv3/4AkRKM:ARxR9Y5cI1CmVtVpvgL | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (14cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 54 AntiVirus engines on VirusTotal as malicious |
| watch | Attempts to identify installed AV products by installation directory |
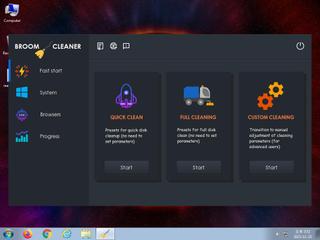
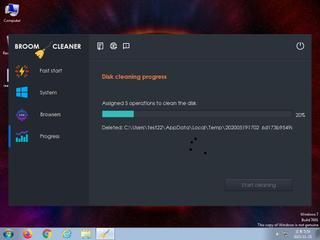
| watch | Deletes a large number of files from the system indicative of ransomware |
| watch | Deletes executed files from disk |
| watch | Detects VirtualBox through the presence of a file |
| watch | Drops 156 unknown file mime types indicative of ransomware writing encrypted files back to disk |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (27cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | NSIS_Installer | Null Soft Installer | binaries (download) |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| info | bmp_file_format | bmp file format | binaries (download) |
| info | CAB_file_format | CAB archive file | binaries (download) |
| info | chm_file_format | chm file format | binaries (download) |
| info | docx | Word 2007 file format detection | binaries (download) |
| info | icon_file_format | icon file format | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (download) |
| info | JPEG_Format_Zero | JPEG Format | binaries (download) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | PNG_Format_Zero | PNG Format | binaries (download) |
| info | zip_file_format | ZIP file format | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none