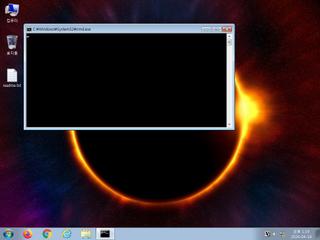
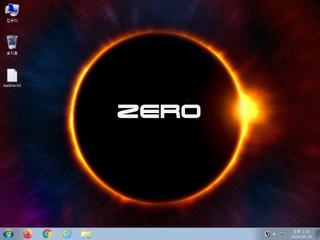
ScreenShot
| Created | 2024.04.19 13:21 | Machine | s1_win7_x6402 |
| Filename | SA162.pdf.lnk | ||
| Type | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has command line arguments, Icon number=13, Archive, ctime=Fri May 7 23:13:59 2021, mtime=Fri May 7 23:13:59 2021, atime=Fri May 7 23:1 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 19 detected (Pantera, gen111, a variant of Generik, HGDTHWW, Mshta, CLASSIC, LnkRun, Detected, ai score=81) | ||
| md5 | f9f276db97c371b83765a24ee1d14d66 | ||
| sha256 | 57aa9cce85c62c5f29fd37a5cc02f11d1f7c0ecb73a8e17688bae859d4695f42 | ||
| ssdeep | 24:8faNkDmgih41Av94zcuhJBkOtp+/4P+8PxkSlqdd79dsW28mT84abtl868z7m:8famDmCC9AJL77mSgdJ9pn4a46q | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (28cnts)
| Level | Description |
|---|---|
| watch | Creates a suspicious Powershell process |
| watch | Disables proxy possibly for traffic interception |
| watch | File has been identified by 19 AntiVirus engines on VirusTotal as malicious |
| watch | Modifies proxy override settings possibly for traffic interception |
| watch | Network communications indicative of a potential document or script payload download was initiated by the process powershell.exe |
| watch | One or more non-whitelisted processes were created |
| watch | Putty Files |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | The process powershell.exe wrote an executable file to disk |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An executable file was downloaded by the process mshta.exe |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Drops an executable to the user AppData folder |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Poweshell is sending data to a remote host |
| notice | URL downloaded by powershell script |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (17cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsPE32 | (no description) | binaries (download) |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (upload) |
| info | Lnk_Format_Zero | LNK Format | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PowerShell | PowerShell script | scripts |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO Packed Executable Download
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Packed Executable Download
ET POLICY PE EXE or DLL Windows file download HTTP