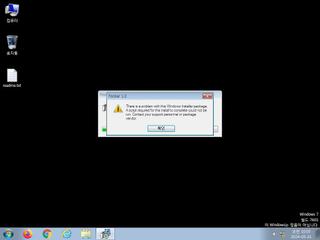
ScreenShot
| Created | 2024.05.31 10:14 | Machine | s1_win7_x6401 |
| Filename | reverse_http.msi | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Foobar 1.0, Author: Acme Ltd., Keywords: Installer, Comments: This installer database contains the logic a | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | |||
| md5 | c16d8d4e2bcfb175ad690580b3502218 | ||
| sha256 | 641f430318f84b8d9b69ba530e13ed5d757b99a58de0ac22a82f1afad82b6918 | ||
| ssdeep | 384:iHpe4ZvJXK7gzFM7Wu86giNHoXgZs+5BCq26yy3M5BCqPN:Zmxa7gBMyuBPDCUyWMDC | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (8cnts)
| Level | Description |
|---|---|
| danger | Connects to IP addresses that are no longer responding to requests (legitimate services will remain up-and-running usually) |
| watch | Communicates with host for which no DNS query was performed |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |