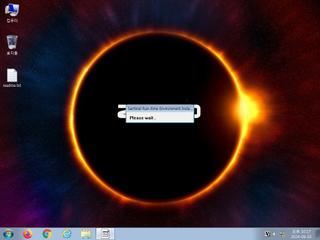
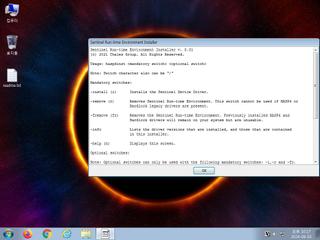
ScreenShot
| Created | 2024.06.03 22:19 | Machine | s1_win7_x6402 |
| Filename | haspdinst_8_31+(2).exe | ||
| Type | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 2 detected (Malicious, score) | ||
| md5 | 235623c73f1d0283860da85f75d41500 | ||
| sha256 | 1718be91005a0440dcb9502da39318295db19fede34d2528ddc4f0b4d5485cbd | ||
| ssdeep | 786432:9NcVQMBtzAwI+pKvU6J5NUoPfb/Jrbp+N2dUbEqqX4d2O:9jMBVDpQxJ5NUoPj/JPRCExO | ||
| imphash | ca3b55b8afa5fa8558364aa0b5fc8540 | ||
| impfuzzy | 48:BGTrzkylSe46U0Xl0Q5Ak5SvKRFEzACLiXo4x5nB/1ES5CWIbnx9LhcSGx9OtcJI:+y4hvIbzLhcjx9Acqc0FGpw | ||
Network IP location
Signature (7cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | File has been identified by 2 AntiVirus engines on VirusTotal as malicious |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (21cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (upload) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (upload) |
| info | CAB_file_format | CAB archive file | binaries (download) |
| info | CAB_file_format | CAB archive file | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
USER32.dll
0x40f1a0 GetMessageA
0x40f1a4 TranslateMessage
0x40f1a8 DispatchMessageA
0x40f1ac GetDesktopWindow
0x40f1b0 CopyRect
0x40f1b4 OffsetRect
0x40f1b8 SetWindowPos
0x40f1bc LoadIconA
0x40f1c0 LoadCursorA
0x40f1c4 DialogBoxParamA
0x40f1c8 CreateWindowExW
0x40f1cc CreateWindowExA
0x40f1d0 RegisterClassA
0x40f1d4 ExitWindowsEx
0x40f1d8 SetWindowTextW
0x40f1dc ScreenToClient
0x40f1e0 EndDialog
0x40f1e4 ShowWindow
0x40f1e8 GetDlgItem
0x40f1ec GetSystemMetrics
0x40f1f0 EnableWindow
0x40f1f4 GetTabbedTextExtentA
0x40f1f8 SetWindowTextA
0x40f1fc GetWindowRect
0x40f200 MoveWindow
0x40f204 SendMessageA
0x40f208 GetClientRect
0x40f20c GetDC
0x40f210 SystemParametersInfoA
0x40f214 ReleaseDC
0x40f218 PostQuitMessage
0x40f21c DefWindowProcA
0x40f220 BeginPaint
0x40f224 EndPaint
0x40f228 UpdateWindow
0x40f22c InvalidateRect
ADVAPI32.dll
0x40f000 AdjustTokenPrivileges
0x40f004 LookupPrivilegeValueA
0x40f008 OpenProcessToken
GDI32.dll
0x40f010 TextOutA
0x40f014 SetBkMode
0x40f018 SetBkColor
0x40f01c DeleteObject
0x40f020 GetTextExtentPoint32A
0x40f024 SelectObject
0x40f028 CreateFontIndirectA
0x40f02c LPtoDP
0x40f030 GetTextExtentPointW
0x40f034 CreateFontW
0x40f038 GetDeviceCaps
SHELL32.dll
0x40f194 ShellExecuteW
0x40f198 SHGetFolderPathA
KERNEL32.dll
0x40f040 GetOEMCP
0x40f044 GetACP
0x40f048 InitializeCriticalSection
0x40f04c SetFilePointer
0x40f050 ReadFile
0x40f054 GetCPInfo
0x40f058 SetHandleCount
0x40f05c GetEnvironmentStringsW
0x40f060 FreeEnvironmentStringsW
0x40f064 GetEnvironmentStrings
0x40f068 FreeEnvironmentStringsA
0x40f06c UnhandledExceptionFilter
0x40f070 QueryPerformanceCounter
0x40f074 GetTickCount
0x40f078 GetCurrentProcessId
0x40f07c GetSystemTimeAsFileTime
0x40f080 GetLocaleInfoA
0x40f084 GetStringTypeA
0x40f088 GetStringTypeW
0x40f08c HeapSize
0x40f090 SetStdHandle
0x40f094 FlushFileBuffers
0x40f098 CreateFileW
0x40f09c SetEndOfFile
0x40f0a0 GetFileType
0x40f0a4 WaitForSingleObject
0x40f0a8 GetStdHandle
0x40f0ac WriteFile
0x40f0b0 CloseHandle
0x40f0b4 GetModuleFileNameA
0x40f0b8 WideCharToMultiByte
0x40f0bc GetModuleFileNameW
0x40f0c0 Sleep
0x40f0c4 GetLastError
0x40f0c8 GetVersionExA
0x40f0cc MultiByteToWideChar
0x40f0d0 CreateFileA
0x40f0d4 GetWindowsDirectoryA
0x40f0d8 GetTempPathA
0x40f0dc LocalFree
0x40f0e0 GetLocalTime
0x40f0e4 LocalAlloc
0x40f0e8 GetModuleHandleA
0x40f0ec GetProcAddress
0x40f0f0 GetModuleHandleW
0x40f0f4 ExitThread
0x40f0f8 ExitProcess
0x40f0fc GetCurrentProcess
0x40f100 LoadLibraryW
0x40f104 SetLastError
0x40f108 OutputDebugStringA
0x40f10c LoadLibraryA
0x40f110 MulDiv
0x40f114 MoveFileExA
0x40f118 DeleteFileW
0x40f11c FreeLibrary
0x40f120 TerminateThread
0x40f124 CreateThread
0x40f128 CreateMutexA
0x40f12c GetSystemInfo
0x40f130 RtlUnwind
0x40f134 HeapAlloc
0x40f138 HeapReAlloc
0x40f13c TerminateProcess
0x40f140 GetStartupInfoA
0x40f144 GetCommandLineA
0x40f148 HeapFree
0x40f14c EnterCriticalSection
0x40f150 LeaveCriticalSection
0x40f154 InterlockedExchange
0x40f158 VirtualQuery
0x40f15c VirtualProtect
0x40f160 VirtualAlloc
0x40f164 LCMapStringA
0x40f168 LCMapStringW
0x40f16c TlsAlloc
0x40f170 GetCurrentThreadId
0x40f174 TlsFree
0x40f178 TlsSetValue
0x40f17c TlsGetValue
0x40f180 DeleteCriticalSection
0x40f184 HeapDestroy
0x40f188 HeapCreate
0x40f18c VirtualFree
EAT(Export Address Table) is none
USER32.dll
0x40f1a0 GetMessageA
0x40f1a4 TranslateMessage
0x40f1a8 DispatchMessageA
0x40f1ac GetDesktopWindow
0x40f1b0 CopyRect
0x40f1b4 OffsetRect
0x40f1b8 SetWindowPos
0x40f1bc LoadIconA
0x40f1c0 LoadCursorA
0x40f1c4 DialogBoxParamA
0x40f1c8 CreateWindowExW
0x40f1cc CreateWindowExA
0x40f1d0 RegisterClassA
0x40f1d4 ExitWindowsEx
0x40f1d8 SetWindowTextW
0x40f1dc ScreenToClient
0x40f1e0 EndDialog
0x40f1e4 ShowWindow
0x40f1e8 GetDlgItem
0x40f1ec GetSystemMetrics
0x40f1f0 EnableWindow
0x40f1f4 GetTabbedTextExtentA
0x40f1f8 SetWindowTextA
0x40f1fc GetWindowRect
0x40f200 MoveWindow
0x40f204 SendMessageA
0x40f208 GetClientRect
0x40f20c GetDC
0x40f210 SystemParametersInfoA
0x40f214 ReleaseDC
0x40f218 PostQuitMessage
0x40f21c DefWindowProcA
0x40f220 BeginPaint
0x40f224 EndPaint
0x40f228 UpdateWindow
0x40f22c InvalidateRect
ADVAPI32.dll
0x40f000 AdjustTokenPrivileges
0x40f004 LookupPrivilegeValueA
0x40f008 OpenProcessToken
GDI32.dll
0x40f010 TextOutA
0x40f014 SetBkMode
0x40f018 SetBkColor
0x40f01c DeleteObject
0x40f020 GetTextExtentPoint32A
0x40f024 SelectObject
0x40f028 CreateFontIndirectA
0x40f02c LPtoDP
0x40f030 GetTextExtentPointW
0x40f034 CreateFontW
0x40f038 GetDeviceCaps
SHELL32.dll
0x40f194 ShellExecuteW
0x40f198 SHGetFolderPathA
KERNEL32.dll
0x40f040 GetOEMCP
0x40f044 GetACP
0x40f048 InitializeCriticalSection
0x40f04c SetFilePointer
0x40f050 ReadFile
0x40f054 GetCPInfo
0x40f058 SetHandleCount
0x40f05c GetEnvironmentStringsW
0x40f060 FreeEnvironmentStringsW
0x40f064 GetEnvironmentStrings
0x40f068 FreeEnvironmentStringsA
0x40f06c UnhandledExceptionFilter
0x40f070 QueryPerformanceCounter
0x40f074 GetTickCount
0x40f078 GetCurrentProcessId
0x40f07c GetSystemTimeAsFileTime
0x40f080 GetLocaleInfoA
0x40f084 GetStringTypeA
0x40f088 GetStringTypeW
0x40f08c HeapSize
0x40f090 SetStdHandle
0x40f094 FlushFileBuffers
0x40f098 CreateFileW
0x40f09c SetEndOfFile
0x40f0a0 GetFileType
0x40f0a4 WaitForSingleObject
0x40f0a8 GetStdHandle
0x40f0ac WriteFile
0x40f0b0 CloseHandle
0x40f0b4 GetModuleFileNameA
0x40f0b8 WideCharToMultiByte
0x40f0bc GetModuleFileNameW
0x40f0c0 Sleep
0x40f0c4 GetLastError
0x40f0c8 GetVersionExA
0x40f0cc MultiByteToWideChar
0x40f0d0 CreateFileA
0x40f0d4 GetWindowsDirectoryA
0x40f0d8 GetTempPathA
0x40f0dc LocalFree
0x40f0e0 GetLocalTime
0x40f0e4 LocalAlloc
0x40f0e8 GetModuleHandleA
0x40f0ec GetProcAddress
0x40f0f0 GetModuleHandleW
0x40f0f4 ExitThread
0x40f0f8 ExitProcess
0x40f0fc GetCurrentProcess
0x40f100 LoadLibraryW
0x40f104 SetLastError
0x40f108 OutputDebugStringA
0x40f10c LoadLibraryA
0x40f110 MulDiv
0x40f114 MoveFileExA
0x40f118 DeleteFileW
0x40f11c FreeLibrary
0x40f120 TerminateThread
0x40f124 CreateThread
0x40f128 CreateMutexA
0x40f12c GetSystemInfo
0x40f130 RtlUnwind
0x40f134 HeapAlloc
0x40f138 HeapReAlloc
0x40f13c TerminateProcess
0x40f140 GetStartupInfoA
0x40f144 GetCommandLineA
0x40f148 HeapFree
0x40f14c EnterCriticalSection
0x40f150 LeaveCriticalSection
0x40f154 InterlockedExchange
0x40f158 VirtualQuery
0x40f15c VirtualProtect
0x40f160 VirtualAlloc
0x40f164 LCMapStringA
0x40f168 LCMapStringW
0x40f16c TlsAlloc
0x40f170 GetCurrentThreadId
0x40f174 TlsFree
0x40f178 TlsSetValue
0x40f17c TlsGetValue
0x40f180 DeleteCriticalSection
0x40f184 HeapDestroy
0x40f188 HeapCreate
0x40f18c VirtualFree
EAT(Export Address Table) is none