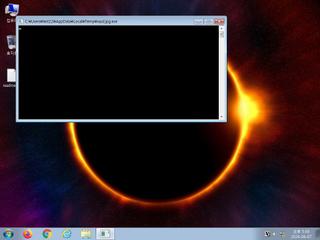
ScreenShot
| Created | 2024.06.07 17:58 | Machine | s1_win7_x6402 |
| Filename | wpd.jpg.exe | ||
| Type | PE32 executable (console) Intel 80386, for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 46 detected (, a variant of Win32/Packed.VMProtect.BB suspicious, Gen:NN.ZexaF.36802.@F0@amAGdVjb, Malicious, unsafe, Trojan ( 0059cf821 ), malicious (high confidence), Generic.mg.1bfe19a314dd31d6, Detected, Artemis!1BFE19A314DD, Gen:Variant.Fragtor.353802 (B), Trojan.Mirai, W32.AIDetectMalware, ML.Attribute.HighConfidence, Trojan.Mirai.Gen, Trojan.Win32.Fragtor.Vt91, malicious.moderate.ml.score, Trojan:Win32/Malgent!MSR, Trojan.VMProtect.Win32.85971, Trojan[Packed]/Win32.VMProtect, malware (ai score=87), TR/AD.Mirai.gvzej, Trojan.Generic@AI.94 (RDML:ey+eAzKln2Fic7TYIF4fVA), VirTool:Win/Malgent, Trj/Agent.RM, MALICIOUS, Trojan.Fragtor.D5660A, Malicious (score: 100), Win32:MalwareX-gen [Trj, Generic.Malware, W32/ABRisk.VGGT-1436, Trojan.Win32.Packed.ca, TROJ_GEN.R002C0DIB23, Static AI - Malicious PE, Gen:Variant.Fragtor.353802, Trojan.Malware.219025362.susgen, Trojan.TR/AD.Mirai.gvzej, Mal/Generic-S, BehavesLike.Win32.Generic.rc) | ||
| md5 | 1bfe19a314dd31d6adda302f177c3b7c | ||
| sha256 | b63ce450e4d34d1cdd727a1a246d38167f45aeacc69d15c6922ef723e49a3cf7 | ||
| ssdeep | 196608:1M6/uTeIz//QEJZe+t6SuqYTFLQmEe2r06+mVWFO5p5adyuFqAHBLgMP:l/YeIzAYe+t1uTJQddQ3Qub | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (26cnts)
| Level | Description |
|---|---|
| danger | Connects to IP addresses that are no longer responding to requests (legitimate services will remain up-and-running usually) |
| watch | A process attempted to delay the analysis task. |
| watch | Communicates with host for which no DNS query was performed |
| watch | Found URLs in memory pointing to an IP address rather than a domain (potentially indicative of Command & Control traffic) |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | Executes one or more WMI queries |
| notice | Foreign language identified in PE resource |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Starts servers listening |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Command line console output was observed |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
| info | The file contains an unknown PE resource name possibly indicative of a packer |
Rules (46cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Network_Downloader | File Downloader | binaries (upload) |
| watch | Network_Downloader | File Downloader | memory |
| watch | schtasks_Zero | task schedule | memory |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | Hijack_Network | Hijack network configuration | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | Is_DotNET_DLL | (no description) | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | vmdetect | Possibly employs anti-virtualization techniques | memory |
| info | win_hook | Affect hook table | memory |
Network (8cnts) ?
Suricata ids
ET SCAN Behavioral Unusual Port 1433 traffic Potential Scan or Infection
ET SCAN Behavioral Unusual Port 445 traffic Potential Scan or Infection
ET SCAN Behavioral Unusual Port 445 traffic Potential Scan or Infection