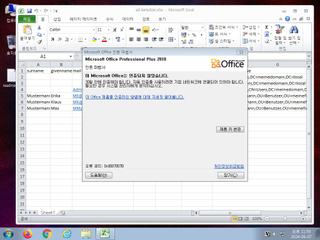
ScreenShot
| Created | 2024.06.08 02:47 | Machine | s1_win7_x6402 |
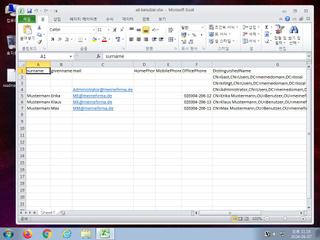
| Filename | ad-benutzer.xlsx | ||
| Type | Microsoft Excel 2007+ | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 25830ea336729f5f8151b25c14ec0bce | ||
| sha256 | a69bab876d9bc107d223b9a3cfbd9d94341f263375d21d27fc70d1ed86e6d016 | ||
| ssdeep | 96:03yBOOa15IsOWFJnQ78tzo+8LMAP3Ok4u1pq6ZR:Qxf15hO0JQQtYMgOLu1pjz | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (8cnts)
| Level | Description |
|---|---|
| watch | Found URLs in memory pointing to an IP address rather than a domain (potentially indicative of Command & Control traffic) |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
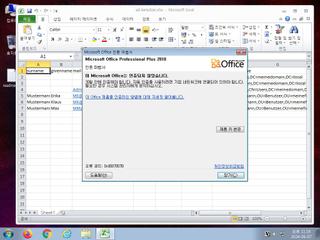
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Yara rule detected in process memory |
| info | One or more processes crashed |
Rules (17cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | schtasks_Zero | task schedule | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | vmdetect | Possibly employs anti-virtualization techniques | memory |
| info | win_hook | Affect hook table | memory |
| info | zip_file_format | ZIP file format | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|