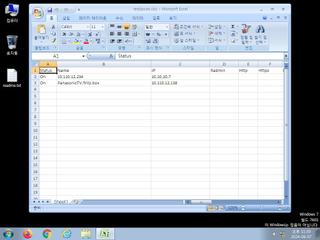
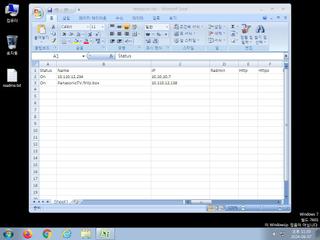
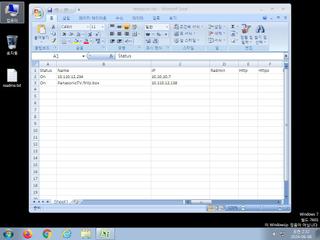
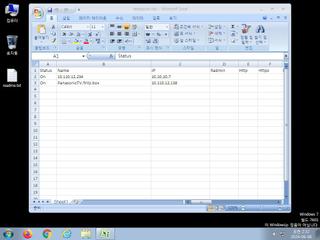
ScreenShot
| Created | 2024.06.08 05:12 | Machine | s1_win7_x6401 |
| Filename | testipscan.xlsx | ||
| Type | Microsoft Excel 2007+ | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 62af5df60e921eb75e8a811735317410 | ||
| sha256 | 8d0cd9f5b8b03aa5a3d4dd2900ea74bd498dbf633b4077c0f6e49e9e7aefb6f4 | ||
| ssdeep | 48:0BgYjNQ5KIBgJD+CtPsWBnafSPgB5PrkpW9yQA7a0rbt++92hmP3Oke9jJts//Sk:03yBOOWBnmrUna0tiAP3OkeJq///v | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (5cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Yara rule detected in process memory |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| info | zip_file_format | ZIP file format | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|