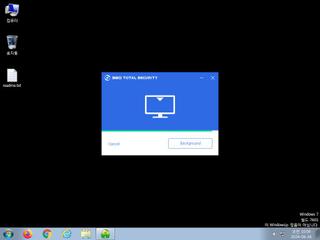
ScreenShot
| Created | 2024.06.16 10:36 | Machine | s1_win7_x6401 |
| Filename | 1234.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | |||
| md5 | 4d85d7bdb9b2d6163ebc289af01f023d | ||
| sha256 | 90ea11576c4edf2d4aa6d7029ad74457980574cef8ee190c8b07f23ff651c84d | ||
| ssdeep | 24576:qL/7n6lbcC8obld1zj1SqdAGFQZIxpC45UJoePZ:q6+C8o5bzjYq+ZIjL5UJoeB | ||
| imphash | 14c198737dea646ad253084b784990ed | ||
| impfuzzy | 24:6D4gmBji3m+yMCrSqwPOYwbu9qJ0oIO3QzsV4WYBMi9lX0+j/a0dbdV40atLAIq1:XgmBD+1LmPpIO383XHdgVt0IqjZuCuW | ||
Network IP location
Signature (15cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| warning | Generates some ICMP traffic |
| watch | Queries information on disks |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for known Chinese AV sofware registry keys |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | Performs some HTTP requests |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Queries for potentially installed applications |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | The file contains an unknown PE resource name possibly indicative of a packer |
| info | This executable has a PDB path |
Rules (39cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | HermeticWiper_Zero | HermeticWiper | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| warning | PhysicalDrive_20181001 | (no description) | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (upload) |
| watch | Network_Downloader | File Downloader | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | CAB_file_format | CAB archive file | binaries (download) |
| info | CAB_file_format | CAB archive file | binaries (upload) |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | DllRegisterServer_Zero | execute regsvr32.exe | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | PNG_Format_Zero | PNG Format | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (28cnts) ?
Suricata ids
ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false)
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false)
ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false)
ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
PE API
IAT(Import Address Table) Library
KERNEL32.dll
0x469000 GetVersionExW
0x469004 GetVersion
0x469008 GetProcAddress
0x46900c GetModuleHandleW
0x469010 FreeLibrary
0x469014 lstrlenW
0x469018 lstrcmpiW
0x46901c LeaveCriticalSection
0x469020 RaiseException
0x469024 EnterCriticalSection
0x469028 GetLastError
0x46902c MultiByteToWideChar
0x469030 SizeofResource
0x469034 LoadResource
0x469038 FindResourceW
0x46903c LoadLibraryExW
0x469040 GetModuleFileNameW
0x469044 InitializeCriticalSection
0x469048 DeleteCriticalSection
0x46904c InterlockedDecrement
0x469050 InterlockedIncrement
0x469054 DebugBreak
0x469058 OutputDebugStringW
0x46905c lstrlenA
0x469060 LockResource
0x469064 FreeResource
0x469068 GetCurrentThreadId
0x46906c GetCommandLineW
0x469070 LocalFree
0x469074 GetSystemDirectoryW
0x469078 CloseHandle
0x46907c ReadFile
0x469080 SetFilePointer
0x469084 CreateFileW
0x469088 GetCurrentProcessId
0x46908c DeviceIoControl
0x469090 GetUserDefaultUILanguage
0x469094 GetTempPathW
0x469098 SetEnvironmentVariableW
0x46909c Sleep
0x4690a0 GetCurrentProcess
0x4690a4 FlushInstructionCache
0x4690a8 SetLastError
0x4690ac GlobalAlloc
0x4690b0 GlobalLock
0x4690b4 GlobalUnlock
0x4690b8 GlobalFree
0x4690bc GetFileSizeEx
0x4690c0 GetLogicalDriveStringsW
0x4690c4 GetDriveTypeW
0x4690c8 GetTempFileNameW
0x4690cc DeleteFileW
0x4690d0 GetDiskFreeSpaceExW
0x4690d4 QueryDosDeviceW
0x4690d8 OpenProcess
0x4690dc MulDiv
0x4690e0 GetPrivateProfileStringW
0x4690e4 GetTickCount
0x4690e8 CreateProcessW
0x4690ec LoadLibraryW
0x4690f0 GetModuleFileNameA
0x4690f4 CreateToolhelp32Snapshot
0x4690f8 MoveFileExW
0x4690fc FindClose
0x469100 GetFullPathNameW
0x469104 FindFirstFileW
0x469108 lstrcpyW
0x46910c FindNextFileW
0x469110 RemoveDirectoryW
0x469114 FreeConsole
0x469118 Process32FirstW
0x46911c Process32NextW
0x469120 WideCharToMultiByte
0x469124 SetEvent
0x469128 CreateMutexW
0x46912c CreateEventW
0x469130 WaitForSingleObject
0x469134 GetLogicalDrives
0x469138 WriteFile
0x46913c LocalAlloc
0x469140 InterlockedCompareExchange
0x469144 CreateFileA
0x469148 GetFileSize
0x46914c InterlockedExchange
0x469150 LoadLibraryA
0x469154 HeapFree
0x469158 GetProcessHeap
0x46915c HeapAlloc
0x469160 IsProcessorFeaturePresent
0x469164 VirtualFree
0x469168 VirtualAlloc
0x46916c SystemTimeToFileTime
0x469170 GetSystemTimeAsFileTime
0x469174 LocalFileTimeToFileTime
0x469178 SetEndOfFile
0x46917c SetFilePointerEx
0x469180 TlsGetValue
0x469184 TlsSetValue
0x469188 HeapUnlock
0x46918c OpenThread
0x469190 HeapLock
0x469194 HeapWalk
0x469198 ReleaseMutex
0x46919c TlsAlloc
0x4691a0 TlsFree
0x4691a4 lstrcmpA
0x4691a8 lstrcmpiA
0x4691ac TerminateProcess
0x4691b0 UnhandledExceptionFilter
0x4691b4 SetUnhandledExceptionFilter
0x4691b8 IsDebuggerPresent
0x4691bc ExitThread
0x4691c0 CreateThread
0x4691c4 ExitProcess
0x4691c8 GetStartupInfoW
0x4691cc RtlUnwind
0x4691d0 LCMapStringA
0x4691d4 LCMapStringW
0x4691d8 GetCPInfo
0x4691dc HeapReAlloc
0x4691e0 HeapSize
0x4691e4 HeapCreate
0x4691e8 HeapDestroy
0x4691ec GetStdHandle
0x4691f0 GetACP
0x4691f4 GetOEMCP
0x4691f8 IsValidCodePage
0x4691fc GetUserDefaultLCID
0x469200 GetLocaleInfoA
0x469204 EnumSystemLocalesA
0x469208 IsValidLocale
0x46920c GetStringTypeA
0x469210 GetStringTypeW
0x469214 InitializeCriticalSectionAndSpinCount
0x469218 GetConsoleCP
0x46921c GetConsoleMode
0x469220 FlushFileBuffers
0x469224 FreeEnvironmentStringsW
0x469228 GetEnvironmentStringsW
0x46922c SetHandleCount
0x469230 GetFileType
0x469234 GetStartupInfoA
0x469238 QueryPerformanceCounter
0x46923c GetModuleHandleA
0x469240 SetStdHandle
0x469244 GetLocaleInfoW
0x469248 WriteConsoleA
0x46924c GetConsoleOutputCP
0x469250 WriteConsoleW
0x469254 FindResourceExW
EAT(Export Address Table) is none
KERNEL32.dll
0x469000 GetVersionExW
0x469004 GetVersion
0x469008 GetProcAddress
0x46900c GetModuleHandleW
0x469010 FreeLibrary
0x469014 lstrlenW
0x469018 lstrcmpiW
0x46901c LeaveCriticalSection
0x469020 RaiseException
0x469024 EnterCriticalSection
0x469028 GetLastError
0x46902c MultiByteToWideChar
0x469030 SizeofResource
0x469034 LoadResource
0x469038 FindResourceW
0x46903c LoadLibraryExW
0x469040 GetModuleFileNameW
0x469044 InitializeCriticalSection
0x469048 DeleteCriticalSection
0x46904c InterlockedDecrement
0x469050 InterlockedIncrement
0x469054 DebugBreak
0x469058 OutputDebugStringW
0x46905c lstrlenA
0x469060 LockResource
0x469064 FreeResource
0x469068 GetCurrentThreadId
0x46906c GetCommandLineW
0x469070 LocalFree
0x469074 GetSystemDirectoryW
0x469078 CloseHandle
0x46907c ReadFile
0x469080 SetFilePointer
0x469084 CreateFileW
0x469088 GetCurrentProcessId
0x46908c DeviceIoControl
0x469090 GetUserDefaultUILanguage
0x469094 GetTempPathW
0x469098 SetEnvironmentVariableW
0x46909c Sleep
0x4690a0 GetCurrentProcess
0x4690a4 FlushInstructionCache
0x4690a8 SetLastError
0x4690ac GlobalAlloc
0x4690b0 GlobalLock
0x4690b4 GlobalUnlock
0x4690b8 GlobalFree
0x4690bc GetFileSizeEx
0x4690c0 GetLogicalDriveStringsW
0x4690c4 GetDriveTypeW
0x4690c8 GetTempFileNameW
0x4690cc DeleteFileW
0x4690d0 GetDiskFreeSpaceExW
0x4690d4 QueryDosDeviceW
0x4690d8 OpenProcess
0x4690dc MulDiv
0x4690e0 GetPrivateProfileStringW
0x4690e4 GetTickCount
0x4690e8 CreateProcessW
0x4690ec LoadLibraryW
0x4690f0 GetModuleFileNameA
0x4690f4 CreateToolhelp32Snapshot
0x4690f8 MoveFileExW
0x4690fc FindClose
0x469100 GetFullPathNameW
0x469104 FindFirstFileW
0x469108 lstrcpyW
0x46910c FindNextFileW
0x469110 RemoveDirectoryW
0x469114 FreeConsole
0x469118 Process32FirstW
0x46911c Process32NextW
0x469120 WideCharToMultiByte
0x469124 SetEvent
0x469128 CreateMutexW
0x46912c CreateEventW
0x469130 WaitForSingleObject
0x469134 GetLogicalDrives
0x469138 WriteFile
0x46913c LocalAlloc
0x469140 InterlockedCompareExchange
0x469144 CreateFileA
0x469148 GetFileSize
0x46914c InterlockedExchange
0x469150 LoadLibraryA
0x469154 HeapFree
0x469158 GetProcessHeap
0x46915c HeapAlloc
0x469160 IsProcessorFeaturePresent
0x469164 VirtualFree
0x469168 VirtualAlloc
0x46916c SystemTimeToFileTime
0x469170 GetSystemTimeAsFileTime
0x469174 LocalFileTimeToFileTime
0x469178 SetEndOfFile
0x46917c SetFilePointerEx
0x469180 TlsGetValue
0x469184 TlsSetValue
0x469188 HeapUnlock
0x46918c OpenThread
0x469190 HeapLock
0x469194 HeapWalk
0x469198 ReleaseMutex
0x46919c TlsAlloc
0x4691a0 TlsFree
0x4691a4 lstrcmpA
0x4691a8 lstrcmpiA
0x4691ac TerminateProcess
0x4691b0 UnhandledExceptionFilter
0x4691b4 SetUnhandledExceptionFilter
0x4691b8 IsDebuggerPresent
0x4691bc ExitThread
0x4691c0 CreateThread
0x4691c4 ExitProcess
0x4691c8 GetStartupInfoW
0x4691cc RtlUnwind
0x4691d0 LCMapStringA
0x4691d4 LCMapStringW
0x4691d8 GetCPInfo
0x4691dc HeapReAlloc
0x4691e0 HeapSize
0x4691e4 HeapCreate
0x4691e8 HeapDestroy
0x4691ec GetStdHandle
0x4691f0 GetACP
0x4691f4 GetOEMCP
0x4691f8 IsValidCodePage
0x4691fc GetUserDefaultLCID
0x469200 GetLocaleInfoA
0x469204 EnumSystemLocalesA
0x469208 IsValidLocale
0x46920c GetStringTypeA
0x469210 GetStringTypeW
0x469214 InitializeCriticalSectionAndSpinCount
0x469218 GetConsoleCP
0x46921c GetConsoleMode
0x469220 FlushFileBuffers
0x469224 FreeEnvironmentStringsW
0x469228 GetEnvironmentStringsW
0x46922c SetHandleCount
0x469230 GetFileType
0x469234 GetStartupInfoA
0x469238 QueryPerformanceCounter
0x46923c GetModuleHandleA
0x469240 SetStdHandle
0x469244 GetLocaleInfoW
0x469248 WriteConsoleA
0x46924c GetConsoleOutputCP
0x469250 WriteConsoleW
0x469254 FindResourceExW
EAT(Export Address Table) is none