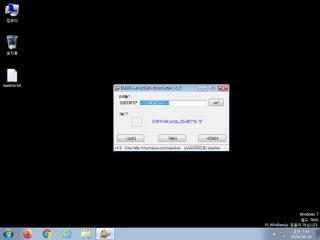
ScreenShot
| Created | 2024.06.18 07:39 | Machine | s1_win7_x6401 |
| Filename | %E5%9B%BE%E8%A1%A8%E6%88%AA%E5%8F%96.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | |||
| md5 | 2a2aee2fb354ba5189af608dd408460a | ||
| sha256 | edb94ff55a2475b119078956db741475395f7f4f597880f747efcd310e429e83 | ||
| ssdeep | 3072:hu+ppLILoxK1/A66MehEqz8uSCrSEtakT+IDwWs8XLYf4z5fKeoutl:huOpLIUJMehEqz8uLxaIDj8f417oS | ||
| imphash | f2a99bb1368a40615d9bd5fe0d2b496d | ||
| impfuzzy | 6:dBJAEHGDzyRlbRmVOZ/EwRgsuVM4CCeGa1KOm3E7s2bBnaOAMyyTch:VA/DzqYOZ9Rgi481K3ERLAITC | ||
Network IP location
Signature (5cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Foreign language identified in PE resource |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks amount of memory in system |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
KERNEL32.DLL
0x4706bc LoadLibraryA
0x4706c0 GetProcAddress
0x4706c4 VirtualProtect
0x4706c8 VirtualAlloc
0x4706cc VirtualFree
0x4706d0 ExitProcess
advapi32.dll
0x4706d8 RegCloseKey
comctl32.dll
0x4706e0 ImageList_Add
comdlg32.dll
0x4706e8 GetSaveFileNameA
gdi32.dll
0x4706f0 SaveDC
oleaut32.dll
0x4706f8 VariantCopy
shell32.dll
0x470700 DragFinish
user32.dll
0x470708 GetDC
version.dll
0x470710 VerQueryValueA
EAT(Export Address Table) is none
KERNEL32.DLL
0x4706bc LoadLibraryA
0x4706c0 GetProcAddress
0x4706c4 VirtualProtect
0x4706c8 VirtualAlloc
0x4706cc VirtualFree
0x4706d0 ExitProcess
advapi32.dll
0x4706d8 RegCloseKey
comctl32.dll
0x4706e0 ImageList_Add
comdlg32.dll
0x4706e8 GetSaveFileNameA
gdi32.dll
0x4706f0 SaveDC
oleaut32.dll
0x4706f8 VariantCopy
shell32.dll
0x470700 DragFinish
user32.dll
0x470708 GetDC
version.dll
0x470710 VerQueryValueA
EAT(Export Address Table) is none