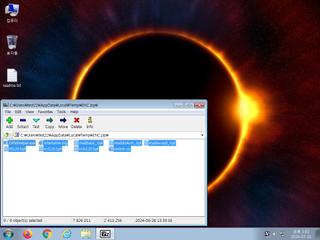
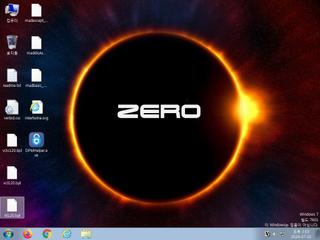
ScreenShot
| Created | 2024.07.01 15:06 | Machine | s1_win7_x6402 |
| Filename | ENC.zip | ||
| Type | Zip archive data, at least v2.0 to extract | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 3 detected (malicious, moderate confidence, Rugmi, ccmw) | ||
| md5 | 34dd73380e19295eef9c195a9f35c9b3 | ||
| sha256 | 208e322fe1e0e726aa69b3ac530da9ad4432dc046202cd06ce655148a73895a8 | ||
| ssdeep | 98304:XFRntzkol6g3ArKTgyI9e8Ki94nnNO+ahXk58GscjseUhtACE9uW:nntlCLenSuN4e6TIL | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (4cnts)
| Level | Description |
|---|---|
| notice | File has been identified by 3 AntiVirus engines on VirusTotal as malicious |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Sends data using the HTTP POST Method |
Rules (1cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | zip_file_format | ZIP file format | binaries (upload) |
Network (10cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)