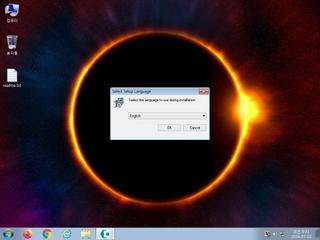
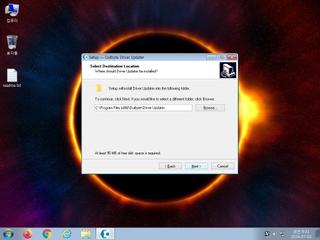
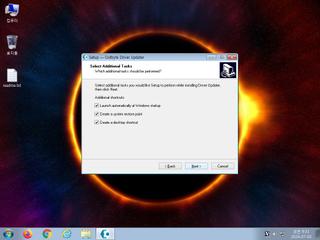
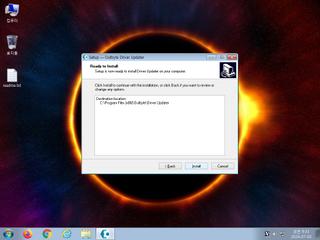
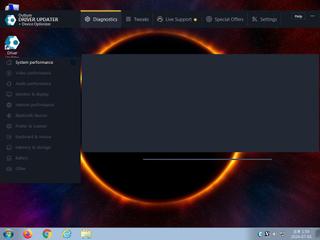
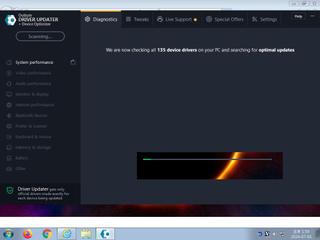
ScreenShot
| Created | 2024.07.03 09:40 | Machine | s1_win7_x6402 |
| Filename | outbyte-driver-updater.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 4 detected (a variant of Generik, IXKVLWK potentially unwanted, Outbyte, grayware, confidence) | ||
| md5 | 19e7819eb886414b6bcab23db00541ec | ||
| sha256 | f42cfe4545c5c62bb19eabd37757c16d3fb69106d0ee25105319d5b15a51d9d2 | ||
| ssdeep | 393216:yRkA1LR74UgmMnRGfjXZYiJwBAOpVFwWJIXMGvmaWQg9m/QOtYzc:BA594xIbhmBAObCWeXMrNm/QOtYg | ||
| imphash | 4d65eb009a5bed7efce0091931f34eb4 | ||
| impfuzzy | 48:jL1ZYHuOC+EkIOhN9VNJPqXnRvEGSjS4FJW/C:jL1ZYOOC+RI0NnNJiXhC | ||
Network IP location
Signature (31cnts)
| Level | Description |
|---|---|
| watch | Attempts to create or modify system certificates |
| watch | Checks the version of Bios |
| watch | Installs itself for autorun at Windows startup |
| watch | Queries information on disks |
| watch | Zeus P2P (Banking Trojan) |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a service |
| notice | Creates a shortcut to an executable file |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | Executes one or more WMI queries |
| notice | Executes one or more WMI queries which can be used to identify virtual machines |
| notice | File has been identified by 4 AntiVirus engines on VirusTotal as malicious |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Queries for potentially installed applications |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Sends data using the HTTP POST Method |
| notice | Steals private information from local Internet browsers |
| notice | Uses Windows utilities for basic Windows functionality |
| info | At least one process apparently crashed during execution |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Command line console output was observed |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
| info | Tries to locate where the browsers are installed |
Rules (26cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | HermeticWiper_Zero | HermeticWiper | binaries (download) |
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | PhysicalDrive_20181001 | (no description) | binaries (download) |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| info | DllRegisterServer_Zero | execute regsvr32.exe | binaries (download) |
| info | ftp_command | ftp command | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (download) |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (download) |
| info | Lnk_Format_Zero | LNK Format | binaries (download) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (10cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO TLS Handshake Failure
ET INFO TLS Handshake Failure
PE API
IAT(Import Address Table) Library
kernel32.dll
0x42d270 SetFileAttributesW
0x42d274 EnterCriticalSection
0x42d278 QueryDosDeviceW
0x42d27c SetFilePointer
0x42d280 GetACP
0x42d284 GetExitCodeProcess
0x42d288 LoadResource
0x42d28c CloseHandle
0x42d290 LocalFree
0x42d294 GetCurrentProcessId
0x42d298 SizeofResource
0x42d29c GetTickCount
0x42d2a0 FindNextFileW
0x42d2a4 GetFullPathNameW
0x42d2a8 VirtualFree
0x42d2ac GetFileSize
0x42d2b0 GetStartupInfoW
0x42d2b4 ExitProcess
0x42d2b8 GetFileAttributesW
0x42d2bc InitializeCriticalSection
0x42d2c0 GetCurrentProcess
0x42d2c4 VirtualAlloc
0x42d2c8 RtlUnwind
0x42d2cc GetCPInfo
0x42d2d0 GetCommandLineW
0x42d2d4 GetSystemInfo
0x42d2d8 GetProcAddress
0x42d2dc LeaveCriticalSection
0x42d2e0 EnumSystemLocalesW
0x42d2e4 GetStdHandle
0x42d2e8 GetLogicalDriveStringsW
0x42d2ec FileTimeToLocalFileTime
0x42d2f0 GetVersionExW
0x42d2f4 VerifyVersionInfoW
0x42d2f8 GetModuleHandleW
0x42d2fc FreeLibrary
0x42d300 GetWindowsDirectoryW
0x42d304 FileTimeToDosDateTime
0x42d308 ReadFile
0x42d30c GetDiskFreeSpaceW
0x42d310 VerSetConditionMask
0x42d314 GetUserDefaultUILanguage
0x42d318 FindFirstFileW
0x42d31c CreateProcessW
0x42d320 UnmapViewOfFile
0x42d324 SetLastError
0x42d328 GetModuleFileNameW
0x42d32c GetLastError
0x42d330 FindResourceW
0x42d334 lstrlenW
0x42d338 SetEndOfFile
0x42d33c QueryPerformanceCounter
0x42d340 CompareStringW
0x42d344 WideCharToMultiByte
0x42d348 MapViewOfFile
0x42d34c MultiByteToWideChar
0x42d350 FindClose
0x42d354 LoadLibraryW
0x42d358 LoadLibraryA
0x42d35c GetVolumeInformationW
0x42d360 ResetEvent
0x42d364 SetEvent
0x42d368 CreateFileW
0x42d36c GetLocaleInfoW
0x42d370 GetDriveTypeW
0x42d374 GetVersion
0x42d378 DeleteFileW
0x42d37c RaiseException
0x42d380 FormatMessageW
0x42d384 SwitchToThread
0x42d388 GetEnvironmentVariableW
0x42d38c GetLocalTime
0x42d390 WaitForSingleObject
0x42d394 WriteFile
0x42d398 CreateFileMappingW
0x42d39c DeleteCriticalSection
0x42d3a0 TlsGetValue
0x42d3a4 IsValidLocale
0x42d3a8 TlsSetValue
0x42d3ac CreateDirectoryW
0x42d3b0 LockResource
0x42d3b4 LoadLibraryExW
0x42d3b8 GetSystemDefaultUILanguage
0x42d3bc EnumCalendarInfoW
0x42d3c0 LocalAlloc
0x42d3c4 RemoveDirectoryW
0x42d3c8 GetCurrentThreadId
0x42d3cc UnhandledExceptionFilter
0x42d3d0 VirtualQuery
0x42d3d4 CreateEventW
0x42d3d8 GetThreadLocale
0x42d3dc Sleep
0x42d3e0 SetThreadLocale
version.dll
0x42d3e8 GetFileVersionInfoSizeW
0x42d3ec VerQueryValueW
0x42d3f0 GetFileVersionInfoW
user32.dll
0x42d3f8 CharUpperBuffW
0x42d3fc CharNextW
0x42d400 MsgWaitForMultipleObjects
0x42d404 TranslateMessage
0x42d408 CharLowerBuffW
0x42d40c LoadStringW
0x42d410 CharUpperW
0x42d414 PeekMessageW
0x42d418 GetSystemMetrics
0x42d41c DispatchMessageW
0x42d420 MessageBoxW
oleaut32.dll
0x42d428 SysAllocStringLen
0x42d42c SysFreeString
0x42d430 SysReAllocStringLen
netapi32.dll
0x42d438 NetWkstaGetInfo
0x42d43c NetApiBufferFree
advapi32.dll
0x42d444 RegQueryValueExW
0x42d448 RegCloseKey
0x42d44c RegOpenKeyExW
EAT(Export Address Table) Library
0x40b598 __dbk_fcall_wrapper
0x42a628 dbkFCallWrapperAddr
kernel32.dll
0x42d270 SetFileAttributesW
0x42d274 EnterCriticalSection
0x42d278 QueryDosDeviceW
0x42d27c SetFilePointer
0x42d280 GetACP
0x42d284 GetExitCodeProcess
0x42d288 LoadResource
0x42d28c CloseHandle
0x42d290 LocalFree
0x42d294 GetCurrentProcessId
0x42d298 SizeofResource
0x42d29c GetTickCount
0x42d2a0 FindNextFileW
0x42d2a4 GetFullPathNameW
0x42d2a8 VirtualFree
0x42d2ac GetFileSize
0x42d2b0 GetStartupInfoW
0x42d2b4 ExitProcess
0x42d2b8 GetFileAttributesW
0x42d2bc InitializeCriticalSection
0x42d2c0 GetCurrentProcess
0x42d2c4 VirtualAlloc
0x42d2c8 RtlUnwind
0x42d2cc GetCPInfo
0x42d2d0 GetCommandLineW
0x42d2d4 GetSystemInfo
0x42d2d8 GetProcAddress
0x42d2dc LeaveCriticalSection
0x42d2e0 EnumSystemLocalesW
0x42d2e4 GetStdHandle
0x42d2e8 GetLogicalDriveStringsW
0x42d2ec FileTimeToLocalFileTime
0x42d2f0 GetVersionExW
0x42d2f4 VerifyVersionInfoW
0x42d2f8 GetModuleHandleW
0x42d2fc FreeLibrary
0x42d300 GetWindowsDirectoryW
0x42d304 FileTimeToDosDateTime
0x42d308 ReadFile
0x42d30c GetDiskFreeSpaceW
0x42d310 VerSetConditionMask
0x42d314 GetUserDefaultUILanguage
0x42d318 FindFirstFileW
0x42d31c CreateProcessW
0x42d320 UnmapViewOfFile
0x42d324 SetLastError
0x42d328 GetModuleFileNameW
0x42d32c GetLastError
0x42d330 FindResourceW
0x42d334 lstrlenW
0x42d338 SetEndOfFile
0x42d33c QueryPerformanceCounter
0x42d340 CompareStringW
0x42d344 WideCharToMultiByte
0x42d348 MapViewOfFile
0x42d34c MultiByteToWideChar
0x42d350 FindClose
0x42d354 LoadLibraryW
0x42d358 LoadLibraryA
0x42d35c GetVolumeInformationW
0x42d360 ResetEvent
0x42d364 SetEvent
0x42d368 CreateFileW
0x42d36c GetLocaleInfoW
0x42d370 GetDriveTypeW
0x42d374 GetVersion
0x42d378 DeleteFileW
0x42d37c RaiseException
0x42d380 FormatMessageW
0x42d384 SwitchToThread
0x42d388 GetEnvironmentVariableW
0x42d38c GetLocalTime
0x42d390 WaitForSingleObject
0x42d394 WriteFile
0x42d398 CreateFileMappingW
0x42d39c DeleteCriticalSection
0x42d3a0 TlsGetValue
0x42d3a4 IsValidLocale
0x42d3a8 TlsSetValue
0x42d3ac CreateDirectoryW
0x42d3b0 LockResource
0x42d3b4 LoadLibraryExW
0x42d3b8 GetSystemDefaultUILanguage
0x42d3bc EnumCalendarInfoW
0x42d3c0 LocalAlloc
0x42d3c4 RemoveDirectoryW
0x42d3c8 GetCurrentThreadId
0x42d3cc UnhandledExceptionFilter
0x42d3d0 VirtualQuery
0x42d3d4 CreateEventW
0x42d3d8 GetThreadLocale
0x42d3dc Sleep
0x42d3e0 SetThreadLocale
version.dll
0x42d3e8 GetFileVersionInfoSizeW
0x42d3ec VerQueryValueW
0x42d3f0 GetFileVersionInfoW
user32.dll
0x42d3f8 CharUpperBuffW
0x42d3fc CharNextW
0x42d400 MsgWaitForMultipleObjects
0x42d404 TranslateMessage
0x42d408 CharLowerBuffW
0x42d40c LoadStringW
0x42d410 CharUpperW
0x42d414 PeekMessageW
0x42d418 GetSystemMetrics
0x42d41c DispatchMessageW
0x42d420 MessageBoxW
oleaut32.dll
0x42d428 SysAllocStringLen
0x42d42c SysFreeString
0x42d430 SysReAllocStringLen
netapi32.dll
0x42d438 NetWkstaGetInfo
0x42d43c NetApiBufferFree
advapi32.dll
0x42d444 RegQueryValueExW
0x42d448 RegCloseKey
0x42d44c RegOpenKeyExW
EAT(Export Address Table) Library
0x40b598 __dbk_fcall_wrapper
0x42a628 dbkFCallWrapperAddr