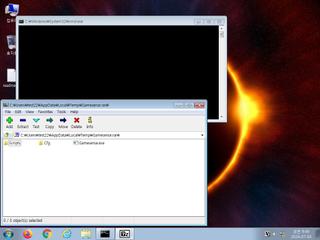
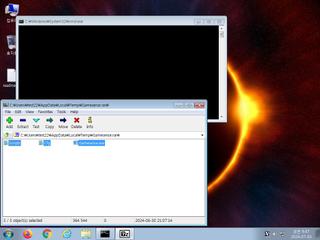
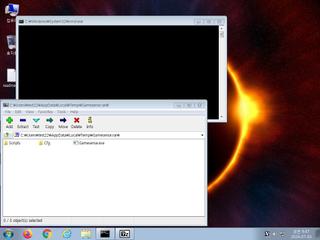
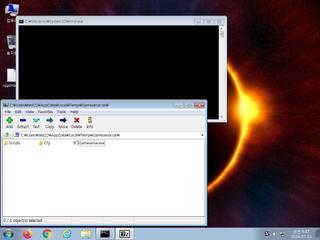
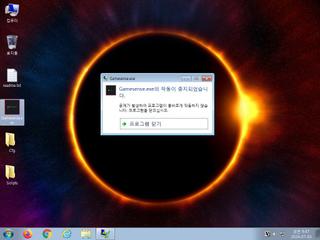
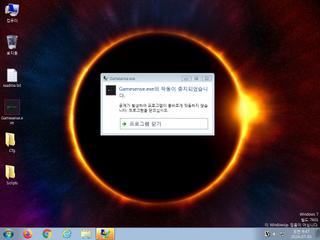
ScreenShot
| Created | 2024.07.03 09:49 | Machine | s1_win7_x6402 |
| Filename | Gamesense.rar | ||
| Type | RAR archive data, v5 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 38 detected (Malicious, score, S31613722, XWorm, Jalapeno, Save, RATX, njRAT, AntiVM, CLASSIC, BladabindiNET, Detected, ai score=81, AsyncRAT, VTQMFW, Eldorado, ZemsilF, wm0@aqMqeNl, Static AI, Malicious Archive, susgen, Bladabindi, SSNY) | ||
| md5 | b1adc1e869b9d40b6d9c8550cd129268 | ||
| sha256 | 991fbd8f8738d75011be7b07ef3054a72e78c59a630fdf5486c57effdeae15d0 | ||
| ssdeep | 1536:EcN3/NiXSb1nHJGTk/zD0TzKkoxPmZq6vsqdTcTEcXLM8S:Ect4Xy9pGTk/n03KkoMZbkAmE+o | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (7cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 38 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (11cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|