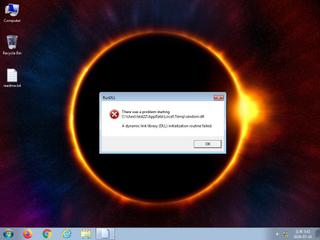
ScreenShot
| Created | 2024.07.14 17:45 | Machine | s1_win7_x6403 |
| Filename | random.dll | ||
| Type | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 19 detected (AIDetectMalware, malicious, high confidence, Expiro, Unsafe, Emotet, FUYR, TrojanX, Mufanom, ccmw, Generic@AI, RDMK, cmRtazomeJBnHH+dvVirYZ7wylUB, Krypt, Detected, ZedlaF, 8w8@a4e0Zde, Kryptik, HVWI, confidence, 100%) | ||
| md5 | f2c158f71dec27759a60227b449e848a | ||
| sha256 | 3e0c8a12a9a72a57857a57ab00a8638719ba96b3d5086836b85a3453459cd5ab | ||
| ssdeep | 49152:GMtP+3WGFsAOuAG8VpAh3P8k3OaNDff6VHscWJLsOlMi144reB0qFQ3CJ6PVDE:3P+3WGp7A91uNDf6pscWpsOlXsqOp | ||
| imphash | 37e89b00b9e59d50b8d5a6dfe0d27623 | ||
| impfuzzy | 24:4tYiyXkqD8J3Jk1tSLfdpVl4JMKgO/1h2n:kYBOa1tSLfrVzKgO/D2 | ||
Network IP location
Signature (3cnts)
| Level | Description |
|---|---|
| watch | File has been identified by 19 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| info | IsDLL | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
KERNEL32.dll
0x1014c008 GetModuleHandleA
0x1014c00c SetPriorityClass
0x1014c010 GetModuleHandleW
0x1014c014 AreFileApisANSI
0x1014c018 GetStringTypeA
0x1014c01c OutputDebugStringA
0x1014c020 GetCPInfo
0x1014c024 InterlockedIncrement
0x1014c028 InterlockedDecrement
0x1014c02c GetACP
0x1014c030 GetOEMCP
0x1014c034 IsValidCodePage
0x1014c038 GetProcAddress
0x1014c03c TlsGetValue
0x1014c040 TlsSetValue
0x1014c044 SetLastError
0x1014c048 GetCurrentThreadId
0x1014c04c GetLastError
0x1014c050 CompareStringW
0x1014c054 TerminateProcess
0x1014c058 GetCurrentProcess
0x1014c05c UnhandledExceptionFilter
0x1014c060 SetUnhandledExceptionFilter
0x1014c064 IsDebuggerPresent
0x1014c068 LCMapStringA
0x1014c06c WideCharToMultiByte
0x1014c070 MultiByteToWideChar
0x1014c074 LCMapStringW
0x1014c078 GetStringTypeW
0x1014c07c LeaveCriticalSection
0x1014c080 EnterCriticalSection
0x1014c084 HeapFree
0x1014c088 Sleep
0x1014c08c ExitProcess
0x1014c090 GetLocaleInfoA
0x1014c094 HeapAlloc
0x1014c098 InitializeCriticalSectionAndSpinCount
0x1014c09c WriteFile
0x1014c0a0 GetStdHandle
0x1014c0a4 GetModuleFileNameA
0x1014c0a8 VirtualFree
0x1014c0ac VirtualAlloc
0x1014c0b0 HeapReAlloc
0x1014c0b4 LoadLibraryA
0x1014c0b8 RtlUnwind
MPRAPI.dll
0x1014c0c0 MprAdminMIBEntrySet
GDI32.dll
0x1014c000 SetDCPenColor
OLEAUT32.dll
0x1014c0c8 GetRecordInfoFromGuids
USER32.dll
0x1014c0d0 GetActiveWindow
0x1014c0d4 SetForegroundWindow
EAT(Export Address Table) Library
0x10270d30 AwcdthodsHlu
KERNEL32.dll
0x1014c008 GetModuleHandleA
0x1014c00c SetPriorityClass
0x1014c010 GetModuleHandleW
0x1014c014 AreFileApisANSI
0x1014c018 GetStringTypeA
0x1014c01c OutputDebugStringA
0x1014c020 GetCPInfo
0x1014c024 InterlockedIncrement
0x1014c028 InterlockedDecrement
0x1014c02c GetACP
0x1014c030 GetOEMCP
0x1014c034 IsValidCodePage
0x1014c038 GetProcAddress
0x1014c03c TlsGetValue
0x1014c040 TlsSetValue
0x1014c044 SetLastError
0x1014c048 GetCurrentThreadId
0x1014c04c GetLastError
0x1014c050 CompareStringW
0x1014c054 TerminateProcess
0x1014c058 GetCurrentProcess
0x1014c05c UnhandledExceptionFilter
0x1014c060 SetUnhandledExceptionFilter
0x1014c064 IsDebuggerPresent
0x1014c068 LCMapStringA
0x1014c06c WideCharToMultiByte
0x1014c070 MultiByteToWideChar
0x1014c074 LCMapStringW
0x1014c078 GetStringTypeW
0x1014c07c LeaveCriticalSection
0x1014c080 EnterCriticalSection
0x1014c084 HeapFree
0x1014c088 Sleep
0x1014c08c ExitProcess
0x1014c090 GetLocaleInfoA
0x1014c094 HeapAlloc
0x1014c098 InitializeCriticalSectionAndSpinCount
0x1014c09c WriteFile
0x1014c0a0 GetStdHandle
0x1014c0a4 GetModuleFileNameA
0x1014c0a8 VirtualFree
0x1014c0ac VirtualAlloc
0x1014c0b0 HeapReAlloc
0x1014c0b4 LoadLibraryA
0x1014c0b8 RtlUnwind
MPRAPI.dll
0x1014c0c0 MprAdminMIBEntrySet
GDI32.dll
0x1014c000 SetDCPenColor
OLEAUT32.dll
0x1014c0c8 GetRecordInfoFromGuids
USER32.dll
0x1014c0d0 GetActiveWindow
0x1014c0d4 SetForegroundWindow
EAT(Export Address Table) Library
0x10270d30 AwcdthodsHlu