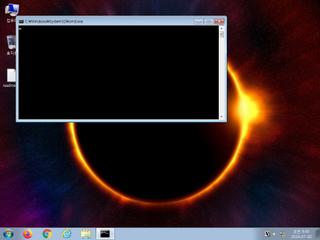
ScreenShot
| Created | 2024.07.30 09:48 | Machine | s1_win7_x6402 |
| Filename | 수정본_20240729.docx.lnk | ||
| Type | MS Windows shortcut, Item id list present, Points to a file or directory, Has command line arguments, Icon number=0, Archive, ctime=Sun Dec 31 15:32:08 1600, mtime=Sun Dec 31 15:32:08 1600, atime=Sun Dec 31 15:32:08 1600, length=0, window=hidenormalshowmi | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 19 detected (Artemis, Pantera, many, WinLNK, LnkGen, ai score=84, Link, MXFlags, Probably Heur, LNKScript) | ||
| md5 | 1bb62f16635e0bcaf7b4ac2c27ceac71 | ||
| sha256 | 6ff5ae0860290f57862f8918e0509c27649ac381ee70a5cb20d6416ec07b4ad5 | ||
| ssdeep | 192:8LpIecDPTwE14cVdVt+87/JbJAChAIQhFsKAlB8T3f52WiqxcCxEFNHxrS+vt:uaDLDVdVt9/JFAA4xEFXS+F | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (18cnts)
| Level | Description |
|---|---|
| watch | Creates a suspicious Powershell process |
| watch | Executes JavaScript in a commandline |
| watch | File has been identified by 19 AntiVirus engines on VirusTotal as malicious |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | The process powershell.exe wrote an executable file to disk |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (13cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (upload) |
| info | Lnk_Format_Zero | LNK Format | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|