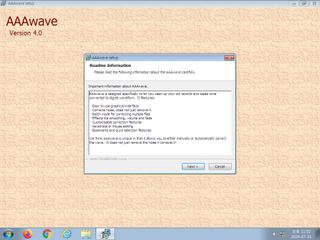
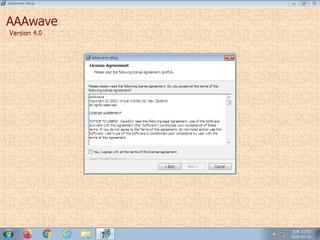
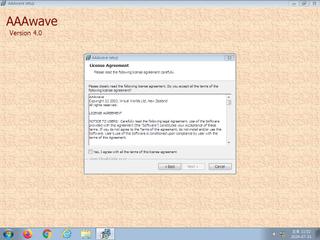
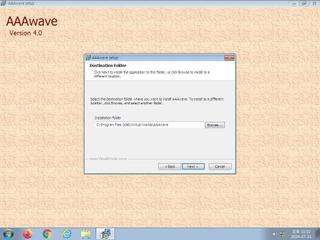
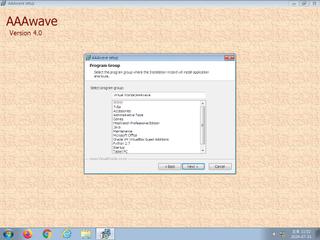
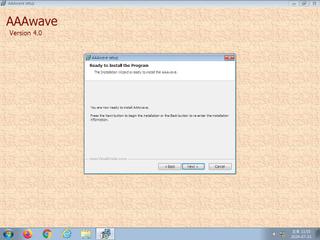
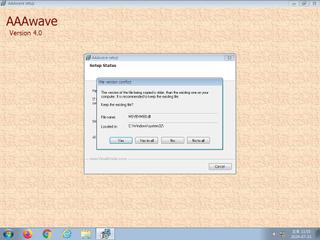
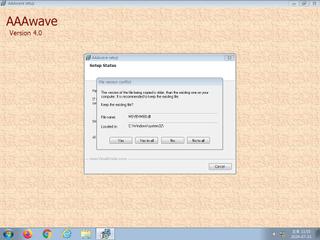
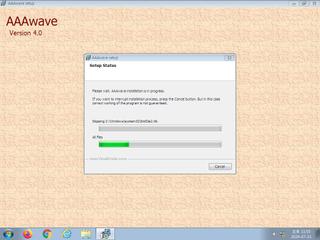
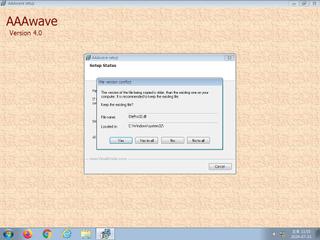
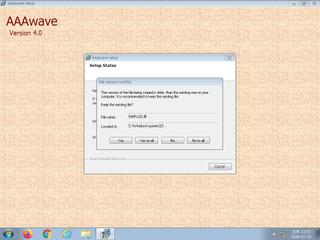
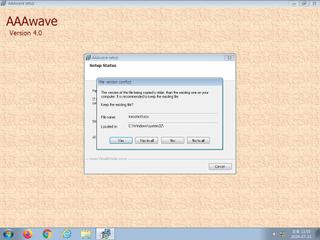
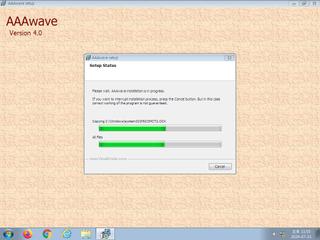
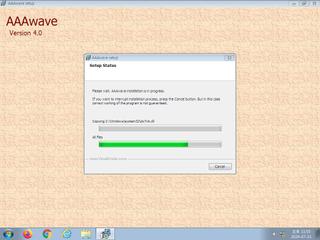
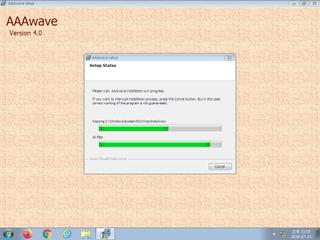
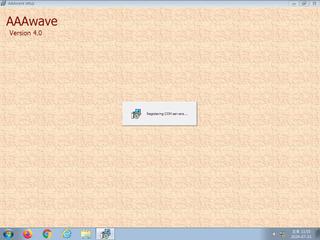
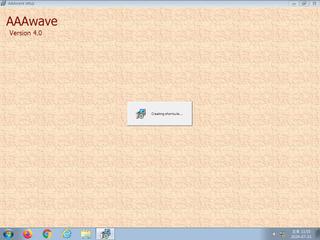
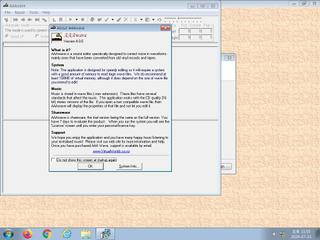
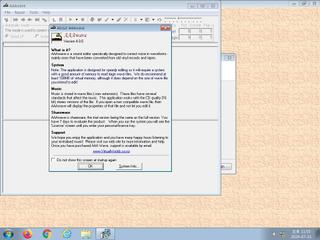
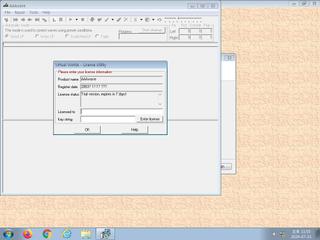
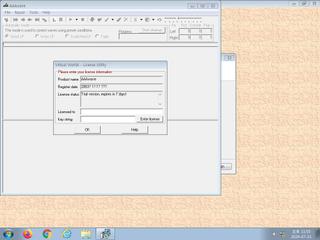
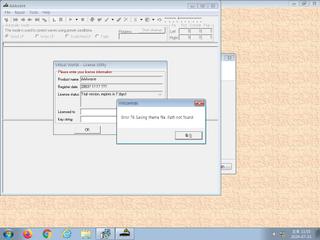
ScreenShot
| Created | 2024.07.31 23:06 | Machine | s1_win7_x6401 |
| Filename | InstallAAAwave.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 1 detected (Malicious, score) | ||
| md5 | 47781e2f67d75de26c08227ef50a1da5 | ||
| sha256 | 499bc6537c074f8e228faa0e1b723726ca1a8e85f817d16c2abf29c1608f60f9 | ||
| ssdeep | 49152:bYB+dd0A75bMXCx5LVkRRpN10BbvQDYMP13rl49tDt1G:bnptbICx56cJuYorlwdtQ | ||
| imphash | 77e87849d40864ce576ee38a20cdccb8 | ||
| impfuzzy | 6:dBJAEHGDvZ/EwRgscFvKO1c9KJAmzRjLbtyBV3LTch:VA/DvZ9RgPcm9xyBxTC | ||
Network IP location
Signature (12cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates a shortcut to an executable file |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | File has been identified by one AntiVirus engine on VirusTotal as malicious |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | The executable is compressed using UPX |
| info | Checks amount of memory in system |
| info | One or more processes crashed |
| info | Queries for the computername |
Rules (20cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Emotet_2_Zero | Win32 Trojan Emotet | binaries (download) |
| danger | Win32_Trojan_Emotet_2_Zero | Win32 Trojan Emotet | binaries (upload) |
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | bmp_file_format | bmp file format | binaries (download) |
| info | DllRegisterServer_Zero | execute regsvr32.exe | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (download) |
| info | Lnk_Format_Zero | LNK Format | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
KERNEL32.DLL
0x455a00 LoadLibraryA
0x455a04 GetProcAddress
0x455a08 ExitProcess
advapi32.dll
0x455a10 RegCloseKey
comctl32.dll
0x455a18 InitCommonControls
gdi32.dll
0x455a20 BitBlt
ole32.dll
0x455a28 CoInitialize
oleaut32.dll
0x455a30 LoadTypeLib
shell32.dll
0x455a38 ShellExecuteA
user32.dll
0x455a40 EndPaint
version.dll
0x455a48 VerQueryValueA
EAT(Export Address Table) is none
KERNEL32.DLL
0x455a00 LoadLibraryA
0x455a04 GetProcAddress
0x455a08 ExitProcess
advapi32.dll
0x455a10 RegCloseKey
comctl32.dll
0x455a18 InitCommonControls
gdi32.dll
0x455a20 BitBlt
ole32.dll
0x455a28 CoInitialize
oleaut32.dll
0x455a30 LoadTypeLib
shell32.dll
0x455a38 ShellExecuteA
user32.dll
0x455a40 EndPaint
version.dll
0x455a48 VerQueryValueA
EAT(Export Address Table) is none