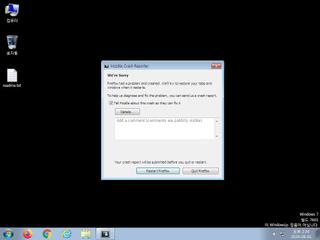
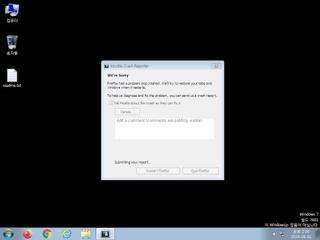
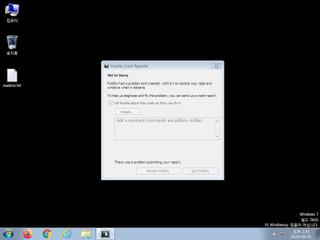
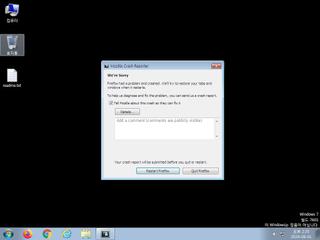
ScreenShot
| Created | 2024.08.01 11:17 | Machine | s1_win7_x6401 |
| Filename | random.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 38 detected (AIDetectMalware, malicious, high confidence, score, Kryptik, Unsafe, Attribute, HighConfidence, Themida, TrojanX, Real Protect, high, Generic ML PUA, Detected, ai score=82, Wacatac, Eldorado, R645974, ZexaF, 2DWaa0YGUCji, Amadey, Probably Heur, ExeHeaderL, Deyma, confidence, 100%) | ||
| md5 | 28700cd817abafa9a16ad89a0f7ffd86 | ||
| sha256 | b6006ca93e5115af8f849d8c9dcba4b1cc6487717d40d6de2bb0cdb795fb6c15 | ||
| ssdeep | 49152:eSUlFq68xolhV4Oq2N8V3Gszu01WM2rlXLWuBrB:eZ4Oq26AW1WM2rlbWIN | ||
| imphash | 2eabe9054cad5152567f0699947a2c5b | ||
| impfuzzy | 3:sBv:A | ||
Network IP location
Signature (45cnts)
| Level | Description |
|---|---|
| danger | Executed a process and injected code into it |
| danger | File has been identified by 38 AntiVirus engines on VirusTotal as malicious |
| watch | Allocates execute permission to another process indicative of possible code injection |
| watch | Appends a known multi-family ransomware file extension to files that have been encrypted |
| watch | Attempts to identify installed AV products by installation directory |
| watch | Checks for the presence of known devices from debuggers and forensic tools |
| watch | Checks for the presence of known windows from debuggers and forensic tools |
| watch | Checks the version of Bios |
| watch | Communicates with host for which no DNS query was performed |
| watch | Detects VMWare through the in instruction feature |
| watch | Found URLs in memory pointing to an IP address rather than a domain (potentially indicative of Command & Control traffic) |
| watch | Installs itself for autorun at Windows startup |
| watch | Manipulates memory of a non-child process indicative of process injection |
| watch | Network activity contains more than one unique useragent |
| watch | One or more non-whitelisted processes were created |
| watch | Potential code injection by writing to the memory of another process |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | A process attempted to delay the analysis task. |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | An executable file was downloaded by the process explorti.exe |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | Expresses interest in specific running processes |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Sends data using the HTTP POST Method |
| notice | Steals private information from local Internet browsers |
| notice | Terminates another process |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
| info | Tries to locate where the browsers are installed |
Rules (50cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Client_SW_User_Data_Stealer | Client_SW_User_Data_Stealer | memory |
| danger | RedLine_Stealer_b_Zero | RedLine stealer | binaries (download) |
| warning | EnigmaProtector_IN | EnigmaProtector | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | infoStealer_browser_Zero | browser info stealer | memory |
| watch | Chrome_User_Data_Check_Zero | Google Chrome User Data Check | memory |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | Network_Downloader | File Downloader | memory |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | BitCoin | Perform crypto currency mining | memory |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | Virtual_currency_Zero | Virtual currency | memory |
| info | vmdetect | Possibly employs anti-virtualization techniques | memory |
| info | win_hook | Affect hook table | memory |
Network (7cnts) ?
Suricata ids
ET DROP Spamhaus DROP Listed Traffic Inbound group 33
ET INFO Executable Download from dotted-quad Host
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2
ET INFO Packed Executable Download
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO Executable Download from dotted-quad Host
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2
ET INFO Packed Executable Download
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
PE API
IAT(Import Address Table) Library
kernel32.dll
0x46a035 lstrcpy
EAT(Export Address Table) is none
kernel32.dll
0x46a035 lstrcpy
EAT(Export Address Table) is none