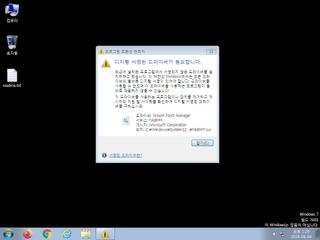
ScreenShot
| Created | 2024.08.04 13:42 | Machine | s1_win7_x6401 |
| Filename | jf.exe | ||
| Type | PE32+ executable (GUI) x86-64, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 47 detected (AIDetectMalware, Reconyc, malicious, moderate confidence, score, GenericKD, Unsafe, Vq9f, Attribute, HighConfidence, a variant of Generik, FWHPHXK, DropperX, pofo, CLOUD, thiwi, Siggen28, Fsysna, R002C0XD524, moderate, Detected, Casdet, Powershell, Chgt, Gencirc, 3MDrTkzBlgA, ai score=82, PossibleThreat, confidence) | ||
| md5 | d161e13cf0731d0b55ad38d6a38cdc21 | ||
| sha256 | 847e71dbcd3917dad9ebc1ad63d497c3257acfeb47164f61423846e1c5dab272 | ||
| ssdeep | 12288:Dkq5oiAasoIqnylPWE8Bgq0VxR9H4kIeguM:DkDiAalPnxtKDfg | ||
| imphash | f12d8b251be05e4edfe87a7ba231b1f4 | ||
| impfuzzy | 6:oxVquVMlEJAKX9C365rBJAEoZ/OEGDzyRLGMQ3QGQsrxKXn:oHElfT3+ABZG/DzdR3QGLrxMn | ||
Network IP location
Signature (34cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 47 AntiVirus engines on VirusTotal as malicious |
| watch | Allocates execute permission to another process indicative of possible code injection |
| watch | Communicates with host for which no DNS query was performed |
| watch | Disables proxy possibly for traffic interception |
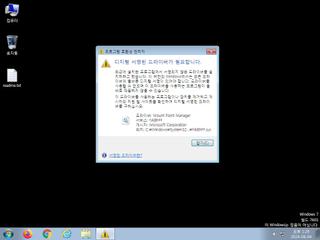
| watch | Drops a binary and executes it |
| watch | Manipulates memory of a non-child process indicative of process injection |
| watch | One or more of the buffers contains an embedded PE file |
| watch | Potential code injection by writing to the memory of another process |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | Tries to detect Sandboxie |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Communication to multiple IPs on high port numbers possibly indicative of a peer-to-peer (P2P) or non-standard command and control protocol |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | Executes one or more WMI queries |
| notice | Executes one or more WMI queries which can be used to identify virtual machines |
| notice | Foreign language identified in PE resource |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Looks up the external IP address |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Sends data using the HTTP POST Method |
| notice | Starts servers listening |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | The executable is compressed using UPX |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | Queries for the computername |
Rules (48cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | CoinMiner_IN | CoinMiner | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | ConfuserEx_Zero | Confuser .NET | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | Network_Downloader | File Downloader | memory |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | Hijack_Network | Hijack network configuration | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
| info | zip_file_format | ZIP file format | binaries (download) |
Network (154cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO Dotted Quad Host ZIP Request
ET INFO Observed External IP Lookup Domain (checkip .amazonaws .com) in TLS SNI
ET INFO External IP Lookup Domain in DNS Lookup (checkip .amazonaws .com)
ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com)
ET INFO Dotted Quad Host ZIP Request
ET INFO Observed External IP Lookup Domain (checkip .amazonaws .com) in TLS SNI
ET INFO External IP Lookup Domain in DNS Lookup (checkip .amazonaws .com)
ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com)
PE API
IAT(Import Address Table) Library
ADVAPI32.dll
0x140107770 CryptEncrypt
COMCTL32.dll
0x140107780 ImageList_Create
CRYPT32.dll
0x140107790 CertOpenStore
GDI32.dll
0x1401077a0 DeleteDC
gdiplus.dll
0x1401077b0 GdipFree
KERNEL32.DLL
0x1401077c0 LoadLibraryA
0x1401077c8 ExitProcess
0x1401077d0 GetProcAddress
0x1401077d8 VirtualProtect
ole32.dll
0x1401077e8 CoUninitialize
USER32.dll
0x1401077f8 GetDC
WLDAP32.dll
0x140107808 None
WS2_32.dll
0x140107818 WSAGetLastError
EAT(Export Address Table) is none
ADVAPI32.dll
0x140107770 CryptEncrypt
COMCTL32.dll
0x140107780 ImageList_Create
CRYPT32.dll
0x140107790 CertOpenStore
GDI32.dll
0x1401077a0 DeleteDC
gdiplus.dll
0x1401077b0 GdipFree
KERNEL32.DLL
0x1401077c0 LoadLibraryA
0x1401077c8 ExitProcess
0x1401077d0 GetProcAddress
0x1401077d8 VirtualProtect
ole32.dll
0x1401077e8 CoUninitialize
USER32.dll
0x1401077f8 GetDC
WLDAP32.dll
0x140107808 None
WS2_32.dll
0x140107818 WSAGetLastError
EAT(Export Address Table) is none