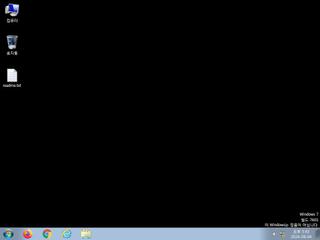
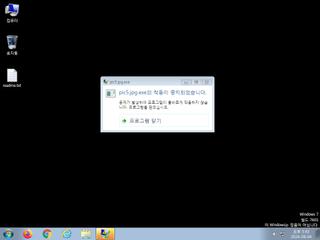
ScreenShot
| Created | 2024.08.04 17:45 | Machine | s1_win7_x6401 |
| Filename | pic5.jpg.exe | ||
| Type | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 21 detected (AIDetectMalware, malicious, high confidence, Unsafe, V1u9, Kryptik, SleepObf, Kryptik@AI, RDML, FvvkDlCfmSj2WKWCy6wOUA, hemnz, SMOKELOADER, YXEHDZ, high, score, confidence, 100%) | ||
| md5 | 85b1854b81d15ac9116aa200304d7ca0 | ||
| sha256 | f1530d12529d8b0ed379457feee1a7cfc223596f455ea0d0771f414699bc88f5 | ||
| ssdeep | 49152:wv9EtY/18WmXsQyVOwJoNWu1vCHdrWTz+pmjjhnlQD38kF:uWm8sQF1vCMe | ||
| imphash | f73673078cd62393b9d4c3d33642daf0 | ||
| impfuzzy | 12:omdyHXVhR9EZ1Sm1XRJRJJcDn5ARZqRLAYPXJDCqV0MH/5XGXgEG6eGJNJmo:FdIXV41/1BfjcDqcLV5X0Mf5XGe6Zpd | ||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 21 AntiVirus engines on VirusTotal as malicious |
| watch | Harvests credentials from local FTP client softwares |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Sends data using the HTTP POST Method |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks amount of memory in system |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (3cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
PE API
IAT(Import Address Table) Library
ADVAPI32.dll
0x1402681a8 RegOpenKeyA
0x1402681b0 RegOpenKeyExW
0x1402681b8 RegOpenKeyW
0x1402681c0 RegQueryInfoKeyW
0x1402681c8 RegQueryMultipleValuesW
0x1402681d0 RegQueryValueA
0x1402681d8 RegQueryValueExW
KERNEL32.dll
0x1402681e8 DeleteCriticalSection
0x1402681f0 EnterCriticalSection
0x1402681f8 GetLastError
0x140268200 GetProcAddress
0x140268208 GetStartupInfoA
0x140268210 InitializeCriticalSection
0x140268218 LeaveCriticalSection
0x140268220 LoadLibraryA
0x140268228 SetUnhandledExceptionFilter
0x140268230 Sleep
0x140268238 TlsAlloc
0x140268240 TlsGetValue
0x140268248 TlsSetValue
0x140268250 VirtualAlloc
0x140268258 VirtualFree
0x140268260 VirtualProtect
0x140268268 VirtualQuery
msvcrt.dll
0x140268278 __C_specific_handler
0x140268280 __initenv
0x140268288 __set_app_type
0x140268290 __setusermatherr
0x140268298 _acmdln
0x1402682a0 _commode
0x1402682a8 _fmode
0x1402682b0 _initterm
0x1402682b8 _ismbblead
0x1402682c0 _onexit
0x1402682c8 abort
0x1402682d0 calloc
0x1402682d8 free
0x1402682e0 memcpy
0x1402682e8 memset
0x1402682f0 strncmp
EAT(Export Address Table) is none
ADVAPI32.dll
0x1402681a8 RegOpenKeyA
0x1402681b0 RegOpenKeyExW
0x1402681b8 RegOpenKeyW
0x1402681c0 RegQueryInfoKeyW
0x1402681c8 RegQueryMultipleValuesW
0x1402681d0 RegQueryValueA
0x1402681d8 RegQueryValueExW
KERNEL32.dll
0x1402681e8 DeleteCriticalSection
0x1402681f0 EnterCriticalSection
0x1402681f8 GetLastError
0x140268200 GetProcAddress
0x140268208 GetStartupInfoA
0x140268210 InitializeCriticalSection
0x140268218 LeaveCriticalSection
0x140268220 LoadLibraryA
0x140268228 SetUnhandledExceptionFilter
0x140268230 Sleep
0x140268238 TlsAlloc
0x140268240 TlsGetValue
0x140268248 TlsSetValue
0x140268250 VirtualAlloc
0x140268258 VirtualFree
0x140268260 VirtualProtect
0x140268268 VirtualQuery
msvcrt.dll
0x140268278 __C_specific_handler
0x140268280 __initenv
0x140268288 __set_app_type
0x140268290 __setusermatherr
0x140268298 _acmdln
0x1402682a0 _commode
0x1402682a8 _fmode
0x1402682b0 _initterm
0x1402682b8 _ismbblead
0x1402682c0 _onexit
0x1402682c8 abort
0x1402682d0 calloc
0x1402682d8 free
0x1402682e0 memcpy
0x1402682e8 memset
0x1402682f0 strncmp
EAT(Export Address Table) is none