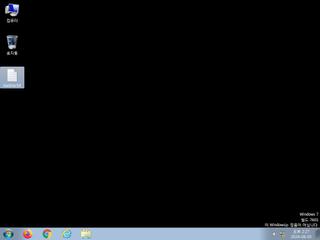
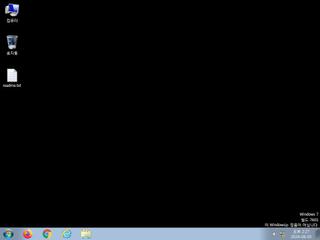
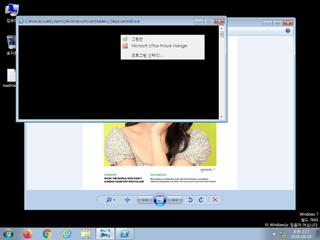
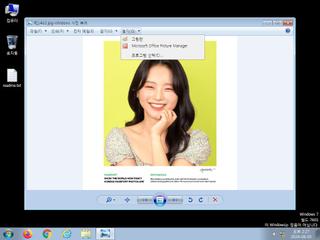
ScreenShot
| Created | 2024.08.05 14:30 | Machine | s1_win7_x6401 |
| Filename | 민혜지2.jse | ||
| Type | ASCII text, with very long lines, with no line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 2 detected (JSRANSOM) | ||
| md5 | 6fba482cb866a3c51dc9063527886f5d | ||
| sha256 | 06e2ab3fe5afc927642244644dfddb0f920ff1ab11c5e5631e26dbd62ed6978a | ||
| ssdeep | 49152:g6WT+aCRHQpNfDaiHMwOgGE2zMXjodR61iVgO9bqJqW17zb0tVqLx2zr+/N7+yaP:r | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (23cnts)
| Level | Description |
|---|---|
| danger | The processes wscript.exe |
| watch | Creates a suspicious Powershell process |
| watch | Drops a binary and executes it |
| watch | Installs itself for autorun at Windows startup |
| watch | One or more non-whitelisted processes were created |
| watch | Potential code injection by writing to the memory of another process |
| watch | Powershell script adds registry entries |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
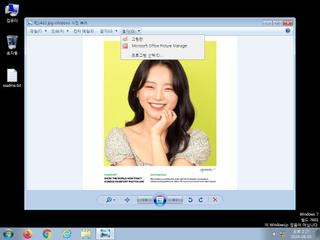
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | File has been identified by 2 AntiVirus engines on VirusTotal as malicious |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Sends data using the HTTP POST Method |
| notice | Uses Windows utilities for basic Windows functionality |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | hide_executable_file | Hide executable file | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | VMProtect_Zero | VMProtect packed file | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (upload) |
| info | IsPE64 | (no description) | binaries (download) |
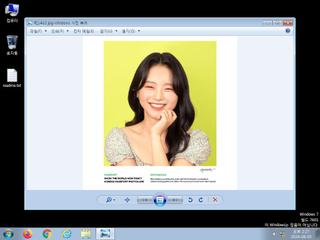
| info | JPEG_Format_Zero | JPEG Format | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |