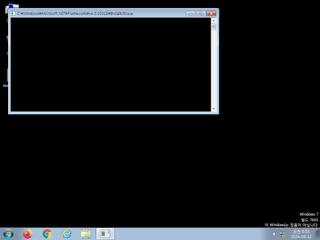
ScreenShot
| Created | 2024.08.12 08:57 | Machine | s1_win7_x6401 |
| Filename | amad.exe | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | |||
| md5 | 33f3040b744a6d2a175866104e3953e4 | ||
| sha256 | 52774cf618d18843fc617ea6e340a5fb1e36559d6c0c372c6c5214ab1fb6e34e | ||
| ssdeep | 24576:XWhAat7ZeOLYOKxBMfRR3JPf77cJCCDQzIP2LBq4rHsq6N53:GhAa5YfuR3N/4DmIPSBXrMq6b3 | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (20cnts)
| Level | Description |
|---|---|
| danger | Executed a process and injected code into it |
| watch | A process attempted to delay the analysis task. |
| watch | Allocates execute permission to another process indicative of possible code injection |
| watch | Attempts to remove evidence of file being downloaded from the Internet |
| watch | Code injection by writing an executable or DLL to the memory of another process |
| watch | Installs itself for autorun at Windows startup |
| watch | Looks for the Windows Idle Time to determine the uptime |
| watch | Potential code injection by writing to the memory of another process |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | Used NtSetContextThread to modify a thread in a remote process indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | One or more potentially interesting buffers were extracted |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (24cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none