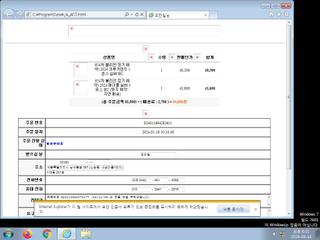
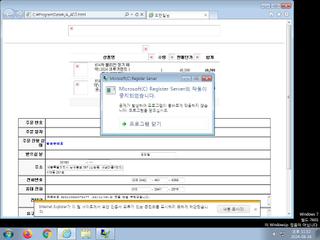
ScreenShot
| Created | 2024.08.16 18:35 | Machine | s1_win7_x6401 |
| Filename | 님.jse | ||
| Type | ASCII text, with very long lines, with no line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 26 detected (Obfuse, SAgent, Siggen25, JSRANSOM, Detected, ai score=81, ABRisk, RDKJ, Javascript) | ||
| md5 | 7756b4230adfa16e18142d1dbe6934af | ||
| sha256 | 6a38c84efe52d8e7298d62809ef59a28b74575f09e7199a6b7f6bf3762a2de44 | ||
| ssdeep | 49152:e3+p0jALGyADS8lucQtMNa9zuOseCHrvl4gZL3NUrSRNkI4aTIyfknngddSCUmF1:q | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (34cnts)
| Level | Description |
|---|---|
| danger | The processes wscript.exe |
| warning | File has been identified by 26 AntiVirus engines on VirusTotal as malicious |
| warning | Generates some ICMP traffic |
| watch | Appends a known multi-family ransomware file extension to files that have been encrypted |
| watch | Communicates with host for which no DNS query was performed |
| watch | Creates a suspicious Powershell process |
| watch | Disables proxy possibly for traffic interception |
| watch | Installs itself for autorun at Windows startup |
| watch | Network activity contains more than one unique useragent |
| watch | One or more non-whitelisted processes were created |
| watch | Potential code injection by writing to the memory of another process |
| watch | Powershell script adds registry entries |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Command line console output was observed |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (26cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | ROMCOM_RAT | Unit 42 observed threat actor Tropical Scorpius using this RAT in operations where also Cuba ransomware was deployed. | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | hide_executable_file | Hide executable file | binaries (download) |
| warning | Suspicious_Obfuscation_Script_2 | Suspicious obfuscation script (e.g. executable files) | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (upload) |
| notice | PDF_Format_Z | PDF Format | binaries (download) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | DllRegisterServer_Zero | execute regsvr32.exe | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE64 | (no description) | binaries (download) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PowerShell | PowerShell script | scripts |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | zip_file_format | ZIP file format | binaries (download) |
Network (8cnts) ?
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)