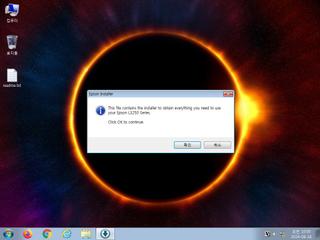
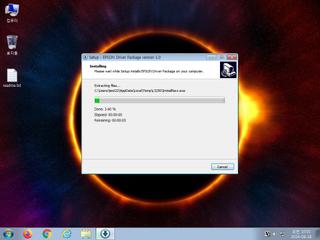
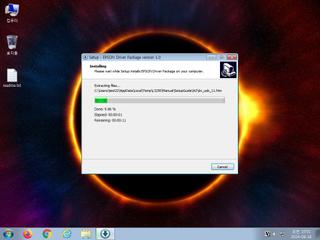
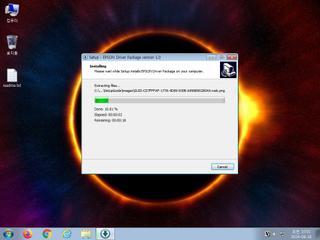
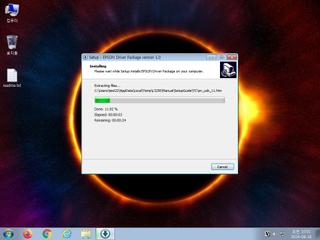
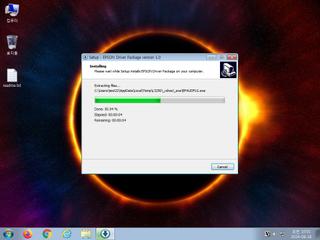
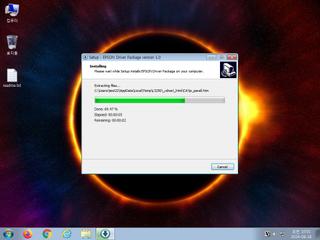
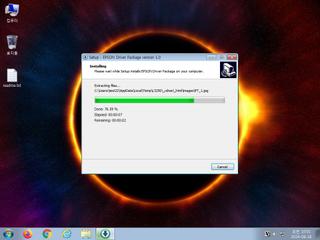
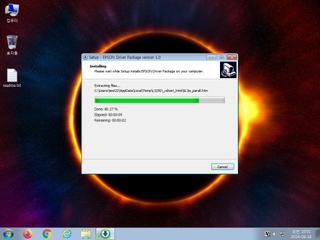
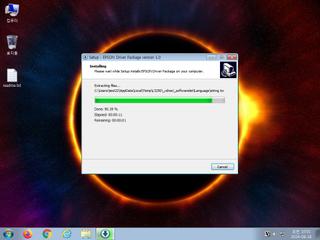
ScreenShot
| Created | 2024.08.18 10:08 | Machine | s1_win7_x6402 |
| Filename | L3250_L3251_Lite_LA.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 23b9be57494e761584989265e5a2dcf3 | ||
| sha256 | a850a227bc2a1de83c1afd170b1ac9b322270b3cbe3f87c9ef7b9e9cc5438024 | ||
| ssdeep | 196608:+ijFL8Ogee3Kc66MUgGSqgIMQSXMWZ9AjnK6c/IT:bjFL8OgeeaqMo5gIMQcZg/cw | ||
| imphash | 20dd26497880c05caed9305b3c8b9109 | ||
| impfuzzy | 48:o4/c+4QjuC5Q4FNO0MeAXGo4E/gjF5J/RscXr9ubudS19WOG/iB:oc94A5TNO0MHYXrMeS1oXiB | ||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| watch | Network activity contains more than one unique useragent |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Drops an executable to the user AppData folder |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Queries for potentially installed applications |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (23cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Schwerer_IN | Schwerer | binaries (download) |
| danger | Win32_Trojan_Emotet_1_Zero | Win32 Trojan Emotet | binaries (download) |
| danger | Win32_Trojan_Emotet_2_Zero | Win32 Trojan Emotet | binaries (download) |
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | icon_file_format | icon file format | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (download) |
| info | JPEG_Format_Zero | JPEG Format | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (download) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | PNG_Format_Zero | PNG Format | binaries (download) |
Network (7cnts) ?
Suricata ids
ET INFO TLS Handshake Failure
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO Observed DNS Query to .biz TLD
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO Observed DNS Query to .biz TLD
PE API
IAT(Import Address Table) Library
oleaut32.dll
0x419304 SysFreeString
0x419308 SysReAllocStringLen
0x41930c SysAllocStringLen
advapi32.dll
0x419314 RegQueryValueExW
0x419318 RegOpenKeyExW
0x41931c RegCloseKey
user32.dll
0x419324 GetKeyboardType
0x419328 LoadStringW
0x41932c MessageBoxA
0x419330 CharNextW
kernel32.dll
0x419338 GetACP
0x41933c Sleep
0x419340 VirtualFree
0x419344 VirtualAlloc
0x419348 GetSystemInfo
0x41934c GetTickCount
0x419350 QueryPerformanceCounter
0x419354 GetVersion
0x419358 GetCurrentThreadId
0x41935c VirtualQuery
0x419360 WideCharToMultiByte
0x419364 MultiByteToWideChar
0x419368 lstrlenW
0x41936c lstrcpynW
0x419370 LoadLibraryExW
0x419374 GetThreadLocale
0x419378 GetStartupInfoA
0x41937c GetProcAddress
0x419380 GetModuleHandleW
0x419384 GetModuleFileNameW
0x419388 GetLocaleInfoW
0x41938c GetCommandLineW
0x419390 FreeLibrary
0x419394 FindFirstFileW
0x419398 FindClose
0x41939c ExitProcess
0x4193a0 WriteFile
0x4193a4 UnhandledExceptionFilter
0x4193a8 RtlUnwind
0x4193ac RaiseException
0x4193b0 GetStdHandle
0x4193b4 CloseHandle
kernel32.dll
0x4193bc TlsSetValue
0x4193c0 TlsGetValue
0x4193c4 LocalAlloc
0x4193c8 GetModuleHandleW
user32.dll
0x4193d0 CreateWindowExW
0x4193d4 TranslateMessage
0x4193d8 SetWindowLongW
0x4193dc PeekMessageW
0x4193e0 MsgWaitForMultipleObjects
0x4193e4 MessageBoxW
0x4193e8 LoadStringW
0x4193ec GetSystemMetrics
0x4193f0 ExitWindowsEx
0x4193f4 DispatchMessageW
0x4193f8 DestroyWindow
0x4193fc CharUpperBuffW
0x419400 CallWindowProcW
kernel32.dll
0x419408 WriteFile
0x41940c WideCharToMultiByte
0x419410 WaitForSingleObject
0x419414 VirtualQuery
0x419418 VirtualProtect
0x41941c VirtualFree
0x419420 VirtualAlloc
0x419424 SizeofResource
0x419428 SignalObjectAndWait
0x41942c SetLastError
0x419430 SetFilePointer
0x419434 SetEvent
0x419438 SetErrorMode
0x41943c SetEndOfFile
0x419440 ResetEvent
0x419444 RemoveDirectoryW
0x419448 ReadFile
0x41944c MultiByteToWideChar
0x419450 LockResource
0x419454 LoadResource
0x419458 LoadLibraryW
0x41945c GetWindowsDirectoryW
0x419460 GetVersionExW
0x419464 GetVersion
0x419468 GetUserDefaultLangID
0x41946c GetThreadLocale
0x419470 GetSystemInfo
0x419474 GetSystemDirectoryW
0x419478 GetStdHandle
0x41947c GetProcAddress
0x419480 GetModuleHandleW
0x419484 GetModuleFileNameW
0x419488 GetLocaleInfoW
0x41948c GetLastError
0x419490 GetFullPathNameW
0x419494 GetFileSize
0x419498 GetFileAttributesW
0x41949c GetExitCodeProcess
0x4194a0 GetEnvironmentVariableW
0x4194a4 GetDiskFreeSpaceW
0x4194a8 GetCurrentProcess
0x4194ac GetCommandLineW
0x4194b0 GetCPInfo
0x4194b4 InterlockedExchange
0x4194b8 InterlockedCompareExchange
0x4194bc FreeLibrary
0x4194c0 FormatMessageW
0x4194c4 FindResourceW
0x4194c8 EnumCalendarInfoW
0x4194cc DeleteFileW
0x4194d0 CreateProcessW
0x4194d4 CreateFileW
0x4194d8 CreateEventW
0x4194dc CreateDirectoryW
0x4194e0 CloseHandle
advapi32.dll
0x4194e8 RegQueryValueExW
0x4194ec RegOpenKeyExW
0x4194f0 RegCloseKey
0x4194f4 OpenProcessToken
0x4194f8 LookupPrivilegeValueW
comctl32.dll
0x419500 InitCommonControls
kernel32.dll
0x419508 Sleep
advapi32.dll
0x419510 AdjustTokenPrivileges
EAT(Export Address Table) is none
oleaut32.dll
0x419304 SysFreeString
0x419308 SysReAllocStringLen
0x41930c SysAllocStringLen
advapi32.dll
0x419314 RegQueryValueExW
0x419318 RegOpenKeyExW
0x41931c RegCloseKey
user32.dll
0x419324 GetKeyboardType
0x419328 LoadStringW
0x41932c MessageBoxA
0x419330 CharNextW
kernel32.dll
0x419338 GetACP
0x41933c Sleep
0x419340 VirtualFree
0x419344 VirtualAlloc
0x419348 GetSystemInfo
0x41934c GetTickCount
0x419350 QueryPerformanceCounter
0x419354 GetVersion
0x419358 GetCurrentThreadId
0x41935c VirtualQuery
0x419360 WideCharToMultiByte
0x419364 MultiByteToWideChar
0x419368 lstrlenW
0x41936c lstrcpynW
0x419370 LoadLibraryExW
0x419374 GetThreadLocale
0x419378 GetStartupInfoA
0x41937c GetProcAddress
0x419380 GetModuleHandleW
0x419384 GetModuleFileNameW
0x419388 GetLocaleInfoW
0x41938c GetCommandLineW
0x419390 FreeLibrary
0x419394 FindFirstFileW
0x419398 FindClose
0x41939c ExitProcess
0x4193a0 WriteFile
0x4193a4 UnhandledExceptionFilter
0x4193a8 RtlUnwind
0x4193ac RaiseException
0x4193b0 GetStdHandle
0x4193b4 CloseHandle
kernel32.dll
0x4193bc TlsSetValue
0x4193c0 TlsGetValue
0x4193c4 LocalAlloc
0x4193c8 GetModuleHandleW
user32.dll
0x4193d0 CreateWindowExW
0x4193d4 TranslateMessage
0x4193d8 SetWindowLongW
0x4193dc PeekMessageW
0x4193e0 MsgWaitForMultipleObjects
0x4193e4 MessageBoxW
0x4193e8 LoadStringW
0x4193ec GetSystemMetrics
0x4193f0 ExitWindowsEx
0x4193f4 DispatchMessageW
0x4193f8 DestroyWindow
0x4193fc CharUpperBuffW
0x419400 CallWindowProcW
kernel32.dll
0x419408 WriteFile
0x41940c WideCharToMultiByte
0x419410 WaitForSingleObject
0x419414 VirtualQuery
0x419418 VirtualProtect
0x41941c VirtualFree
0x419420 VirtualAlloc
0x419424 SizeofResource
0x419428 SignalObjectAndWait
0x41942c SetLastError
0x419430 SetFilePointer
0x419434 SetEvent
0x419438 SetErrorMode
0x41943c SetEndOfFile
0x419440 ResetEvent
0x419444 RemoveDirectoryW
0x419448 ReadFile
0x41944c MultiByteToWideChar
0x419450 LockResource
0x419454 LoadResource
0x419458 LoadLibraryW
0x41945c GetWindowsDirectoryW
0x419460 GetVersionExW
0x419464 GetVersion
0x419468 GetUserDefaultLangID
0x41946c GetThreadLocale
0x419470 GetSystemInfo
0x419474 GetSystemDirectoryW
0x419478 GetStdHandle
0x41947c GetProcAddress
0x419480 GetModuleHandleW
0x419484 GetModuleFileNameW
0x419488 GetLocaleInfoW
0x41948c GetLastError
0x419490 GetFullPathNameW
0x419494 GetFileSize
0x419498 GetFileAttributesW
0x41949c GetExitCodeProcess
0x4194a0 GetEnvironmentVariableW
0x4194a4 GetDiskFreeSpaceW
0x4194a8 GetCurrentProcess
0x4194ac GetCommandLineW
0x4194b0 GetCPInfo
0x4194b4 InterlockedExchange
0x4194b8 InterlockedCompareExchange
0x4194bc FreeLibrary
0x4194c0 FormatMessageW
0x4194c4 FindResourceW
0x4194c8 EnumCalendarInfoW
0x4194cc DeleteFileW
0x4194d0 CreateProcessW
0x4194d4 CreateFileW
0x4194d8 CreateEventW
0x4194dc CreateDirectoryW
0x4194e0 CloseHandle
advapi32.dll
0x4194e8 RegQueryValueExW
0x4194ec RegOpenKeyExW
0x4194f0 RegCloseKey
0x4194f4 OpenProcessToken
0x4194f8 LookupPrivilegeValueW
comctl32.dll
0x419500 InitCommonControls
kernel32.dll
0x419508 Sleep
advapi32.dll
0x419510 AdjustTokenPrivileges
EAT(Export Address Table) is none