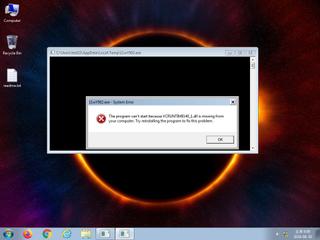
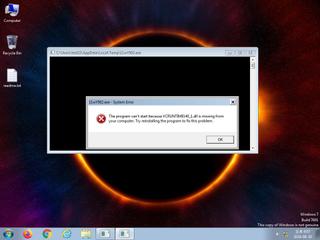
ScreenShot
| Created | 2024.08.30 18:09 | Machine | s1_win7_x6403 |
| Filename | 11wY502.exe | ||
| Type | PE32+ executable (console) x86-64, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 53 detected (AIDetectMalware, VMProtect, malicious, high confidence, score, GenericKD, Unsafe, Save, Attribute, HighConfidence, L suspicious, Artemis, MalwareX, AGEN, Packed2, R002C0RFU24, Real Protect, moderate, VMProtBad, Static AI, Malicious PE, GenKD, Detected, ai score=81, Malware@#2ymuicgoxs2qb, Casdet, Eldorado, susgen, CoinMiner, confidence, 100%) | ||
| md5 | 68d82beae213cad62a60a6df1363b12f | ||
| sha256 | 4caa2065e60833f5fe97ed86c856da9ab5c48c69bafda08c75b7824d74704c18 | ||
| ssdeep | 98304:SENss+BGt8VWWDZdQRSQde1iev5BwGNtTWkIspOMvwNBWFW7zwIfNMgVa:SENR+BHMK6S71RvLrTwwOzNB0W3dNe | ||
| imphash | 18564b1cf3df285f6aada8e4727159f9 | ||
| impfuzzy | 24:a9Qn6E+wSS6oOOJxASgwu5FUBKaQtXJHc9NDI5Q8:8Qn6E7Smb2wzBKnXpcM5Q8 | ||
Network IP location
Signature (4cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 53 AntiVirus engines on VirusTotal as malicious |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | The executable is likely packed with VMProtect |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (5cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Network_Downloader | File Downloader | binaries (upload) |
| watch | VMProtect_Zero | VMProtect packed file | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
KERNEL32.dll
0x140810000 GetFileType
USER32.dll
0x140810010 SetWindowLongA
ADVAPI32.dll
0x140810020 CryptEncrypt
SHELL32.dll
0x140810030 ShellExecuteA
MSVCP140.dll
0x140810040 ?cout@std@@3V?$basic_ostream@DU?$char_traits@D@std@@@1@A
urlmon.dll
0x140810050 URLDownloadToFileA
Normaliz.dll
0x140810060 IdnToAscii
WLDAP32.dll
0x140810070 None
CRYPT32.dll
0x140810080 CertFreeCertificateChain
WS2_32.dll
0x140810090 ntohl
USERENV.dll
0x1408100a0 UnloadUserProfile
VCRUNTIME140.dll
0x1408100b0 __std_exception_destroy
VCRUNTIME140_1.dll
0x1408100c0 __CxxFrameHandler4
api-ms-win-crt-runtime-l1-1-0.dll
0x1408100d0 _initterm_e
api-ms-win-crt-heap-l1-1-0.dll
0x1408100e0 calloc
api-ms-win-crt-utility-l1-1-0.dll
0x1408100f0 rand
api-ms-win-crt-stdio-l1-1-0.dll
0x140810100 feof
api-ms-win-crt-convert-l1-1-0.dll
0x140810110 strtoul
api-ms-win-crt-locale-l1-1-0.dll
0x140810120 _configthreadlocale
api-ms-win-crt-time-l1-1-0.dll
0x140810130 _time64
api-ms-win-crt-string-l1-1-0.dll
0x140810140 strncmp
api-ms-win-crt-filesystem-l1-1-0.dll
0x140810150 _unlink
api-ms-win-crt-math-l1-1-0.dll
0x140810160 __setusermatherr
WTSAPI32.dll
0x140810170 WTSSendMessageW
KERNEL32.dll
0x140810180 GetSystemTimeAsFileTime
USER32.dll
0x140810190 GetUserObjectInformationW
KERNEL32.dll
0x1408101a0 LocalAlloc
0x1408101a8 LocalFree
0x1408101b0 GetModuleFileNameW
0x1408101b8 GetProcessAffinityMask
0x1408101c0 SetProcessAffinityMask
0x1408101c8 SetThreadAffinityMask
0x1408101d0 Sleep
0x1408101d8 ExitProcess
0x1408101e0 FreeLibrary
0x1408101e8 LoadLibraryA
0x1408101f0 GetModuleHandleA
0x1408101f8 GetProcAddress
USER32.dll
0x140810208 GetProcessWindowStation
0x140810210 GetUserObjectInformationW
EAT(Export Address Table) Library
KERNEL32.dll
0x140810000 GetFileType
USER32.dll
0x140810010 SetWindowLongA
ADVAPI32.dll
0x140810020 CryptEncrypt
SHELL32.dll
0x140810030 ShellExecuteA
MSVCP140.dll
0x140810040 ?cout@std@@3V?$basic_ostream@DU?$char_traits@D@std@@@1@A
urlmon.dll
0x140810050 URLDownloadToFileA
Normaliz.dll
0x140810060 IdnToAscii
WLDAP32.dll
0x140810070 None
CRYPT32.dll
0x140810080 CertFreeCertificateChain
WS2_32.dll
0x140810090 ntohl
USERENV.dll
0x1408100a0 UnloadUserProfile
VCRUNTIME140.dll
0x1408100b0 __std_exception_destroy
VCRUNTIME140_1.dll
0x1408100c0 __CxxFrameHandler4
api-ms-win-crt-runtime-l1-1-0.dll
0x1408100d0 _initterm_e
api-ms-win-crt-heap-l1-1-0.dll
0x1408100e0 calloc
api-ms-win-crt-utility-l1-1-0.dll
0x1408100f0 rand
api-ms-win-crt-stdio-l1-1-0.dll
0x140810100 feof
api-ms-win-crt-convert-l1-1-0.dll
0x140810110 strtoul
api-ms-win-crt-locale-l1-1-0.dll
0x140810120 _configthreadlocale
api-ms-win-crt-time-l1-1-0.dll
0x140810130 _time64
api-ms-win-crt-string-l1-1-0.dll
0x140810140 strncmp
api-ms-win-crt-filesystem-l1-1-0.dll
0x140810150 _unlink
api-ms-win-crt-math-l1-1-0.dll
0x140810160 __setusermatherr
WTSAPI32.dll
0x140810170 WTSSendMessageW
KERNEL32.dll
0x140810180 GetSystemTimeAsFileTime
USER32.dll
0x140810190 GetUserObjectInformationW
KERNEL32.dll
0x1408101a0 LocalAlloc
0x1408101a8 LocalFree
0x1408101b0 GetModuleFileNameW
0x1408101b8 GetProcessAffinityMask
0x1408101c0 SetProcessAffinityMask
0x1408101c8 SetThreadAffinityMask
0x1408101d0 Sleep
0x1408101d8 ExitProcess
0x1408101e0 FreeLibrary
0x1408101e8 LoadLibraryA
0x1408101f0 GetModuleHandleA
0x1408101f8 GetProcAddress
USER32.dll
0x140810208 GetProcessWindowStation
0x140810210 GetUserObjectInformationW
EAT(Export Address Table) Library