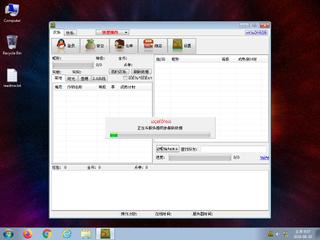
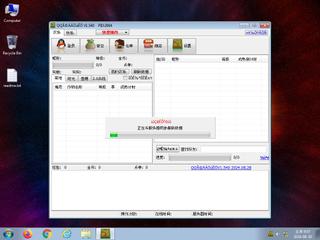
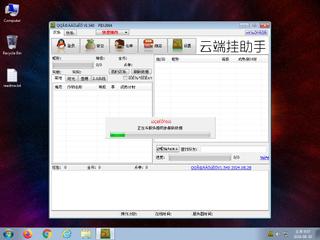
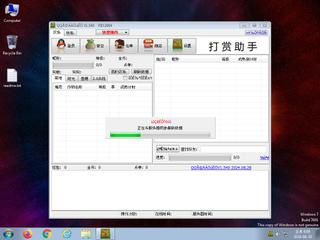
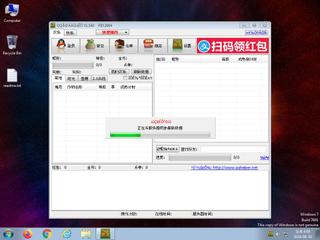
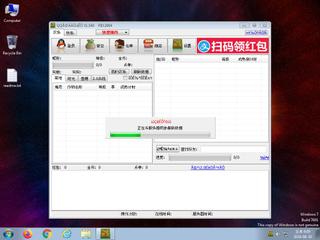
ScreenShot
| Created | 2024.08.30 18:13 | Machine | s1_win7_x6403 |
| Filename | QQHelper_1540.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 13 detected (AIDetectMalware, malicious, moderate confidence, Attribute, HighConfidence, Wacapew, HackTool, R119402, ZelphiF, 1P0ba4GDPTaR, BScope, Click, grayware, confidence, 100%) | ||
| md5 | 5a39d66e2b925f7b7f9f39de2f9c5fa0 | ||
| sha256 | 4f91f9c5d3baf612a1920ae8b2c49a1ee9850d018e308f8e65184a9046138658 | ||
| ssdeep | 49152:5F8IrbBBFJLO55rXuLN+KQDVqNbRSbn+MgaLMNEb:8AN39OjEQDcVRU3Lpb | ||
| imphash | 5e2da45c5591cbc827ecaf03198ed17d | ||
| impfuzzy | 12:mDzjA9A+pZ1nd6w1kTf1E4dGwXukTv13T7E4Cn:mDnWA+pZ1sw1YEqnZTp7Qn | ||
Network IP location
Signature (10cnts)
| Level | Description |
|---|---|
| warning | Generates some ICMP traffic |
| watch | File has been identified by 13 AntiVirus engines on VirusTotal as malicious |
| notice | Foreign language identified in PE resource |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Sends data using the HTTP POST Method |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
| info | The executable uses a known packer |
| info | The file contains an unknown PE resource name possibly indicative of a packer |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | ASPack_Zero | ASPack packed file | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | mzp_file_format | MZP(Delphi) file format | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | url_file_format | Microsoft Windows Internet Shortcut File Format | binaries (download) |
Network (20cnts) ?
Suricata ids
ET POLICY PE EXE or DLL Windows file download HTTP
PE API
IAT(Import Address Table) Library
kernel32.dll
0x963f5c GetProcAddress
0x963f60 GetModuleHandleA
0x963f64 LoadLibraryA
user32.dll
0x964230 GetKeyboardType
advapi32.dll
0x964238 RegQueryValueExA
oleaut32.dll
0x964240 SysFreeString
advapi32.dll
0x964248 RegQueryValueExA
version.dll
0x964250 VerQueryValueA
gdi32.dll
0x964258 UnrealizeObject
user32.dll
0x964260 CreateWindowExA
shell32.dll
0x964268 Shell_NotifyIconA
oleaut32.dll
0x964270 SafeArrayPtrOfIndex
ole32.dll
0x964278 CreateStreamOnHGlobal
oleaut32.dll
0x964280 GetErrorInfo
comctl32.dll
0x964288 _TrackMouseEvent
winspool.drv
0x964290 OpenPrinterA
wininet.dll
0x964298 HttpSendRequestExA
shell32.dll
0x9642a0 SHGetSpecialFolderLocation
wsock32.dll
0x9642a8 WSACleanup
wininet.dll
0x9642b0 InternetCrackUrlA
kernel32
0x9642b8 GetCPInfoExA
winmm.dll
0x9642c0 timeGetTime
EAT(Export Address Table) is none
kernel32.dll
0x963f5c GetProcAddress
0x963f60 GetModuleHandleA
0x963f64 LoadLibraryA
user32.dll
0x964230 GetKeyboardType
advapi32.dll
0x964238 RegQueryValueExA
oleaut32.dll
0x964240 SysFreeString
advapi32.dll
0x964248 RegQueryValueExA
version.dll
0x964250 VerQueryValueA
gdi32.dll
0x964258 UnrealizeObject
user32.dll
0x964260 CreateWindowExA
shell32.dll
0x964268 Shell_NotifyIconA
oleaut32.dll
0x964270 SafeArrayPtrOfIndex
ole32.dll
0x964278 CreateStreamOnHGlobal
oleaut32.dll
0x964280 GetErrorInfo
comctl32.dll
0x964288 _TrackMouseEvent
winspool.drv
0x964290 OpenPrinterA
wininet.dll
0x964298 HttpSendRequestExA
shell32.dll
0x9642a0 SHGetSpecialFolderLocation
wsock32.dll
0x9642a8 WSACleanup
wininet.dll
0x9642b0 InternetCrackUrlA
kernel32
0x9642b8 GetCPInfoExA
winmm.dll
0x9642c0 timeGetTime
EAT(Export Address Table) is none