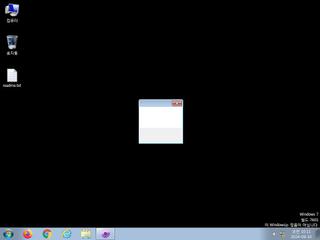
ScreenShot
| Created | 2024.09.10 10:14 | Machine | s1_win7_x6401 |
| Filename | 66dd9b20d75ea_otr.exe#kisotrmeta | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 48 detected (AIDetectMalware, RedLine, Windows, RedLineStealer, Unsafe, Save, Jalapeno, Attribute, HighConfidence, Malicious, SpywareX, Reline, TrojanPSW, Lazy, CLOUD, PRIVATELOADER, YXEIIZ, Real Protect, score, Static AI, Malicious PE, Detected, jnxwr, ai score=80, Sabsik, ABRisk, QHIZ, AgentTesla, QQPass, QQRob, Lflw, susgen, confidence) | ||
| md5 | 805c6dfa454dc8a5538514cc30608f17 | ||
| sha256 | a9bf49d95c4e6d3c9e33e5de82a721ef8f02790daba204d9816b1d581a46b345 | ||
| ssdeep | 12288:vLOPetcpRK87nAPHIlr55kv5ScHSUQmXpCH0S4Mb:vLSpY8ryIlNEUUS4o | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (5cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 48 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
Rules (6cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | RedLine_Stealer_b_Zero | RedLine stealer | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (upload) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none