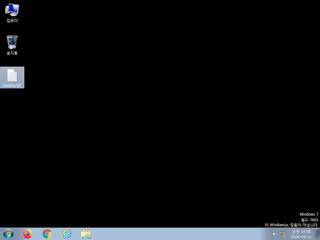
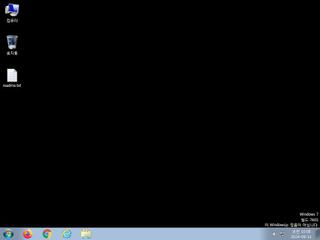
ScreenShot
| Created | 2024.09.11 10:15 | Machine | s1_win7_x6401 |
| Filename | svchost.dll | ||
| Type | PE32+ executable (DLL) (GUI) x86-64, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 23 detected (AIDetectMalware, Cobalt Strike, Malicious, score, Vdte, moderate confidence, Cobalt, CLOUD, AGEN, QMRUFF, Artemis, Ssmw, PossibleThreat) | ||
| md5 | 758efd58932dd3199c315a51c4b103a7 | ||
| sha256 | bf37d4e2861b9f32f706d231974955bdf502c18967c4529a03246d74b093adda | ||
| ssdeep | 192:SjuHTLkz9Kyd1mhAurFdOUhq7G0gAxWw7hAljgF1pELV4y1Drlur+aR4YwVF++z4:SjuHTLScyd1mhAurFdOUhq7G09xWw7hx | ||
| imphash | |||
| impfuzzy | 3:: | ||
Network IP location
Signature (10cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 23 AntiVirus engines on VirusTotal as malicious |
| watch | Communicates with host for which no DNS query was performed |
| watch | Network activity contains more than one unique useragent |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates a suspicious process |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | IsDLL | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
PE API
IAT(Import Address Table) is none
EAT(Export Address Table) Library
0x180001400 debug
EAT(Export Address Table) Library
0x180001400 debug