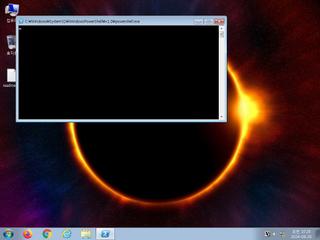
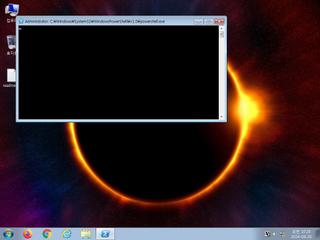
ScreenShot
| Created | 2024.09.20 10:30 | Machine | s1_win7_x6402 |
| Filename | payload.txt.ps1 | ||
| Type | ASCII text, with very long lines | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 37 detected (PowerShell, GenericKD, Save, Cobalt, Rozena, PwrSh, Malicious, score, haktke, CLASSIC, Coblat, COBEACON, SMYXAK, Cometer, Detected, Cobacis, CobaltStrike, S1463, AvosLocker) | ||
| md5 | 888731192f8910e3bfbd4cffaade7d28 | ||
| sha256 | 9c7ba2fdf9025f085d858abff68aaa3a8db07f6b1d657b3c8cdaa3c33aa2644d | ||
| ssdeep | 96:pg5SvvvOmVeLx1Yn64gkjowQYuuA0lgUV0la:SIvOPLx1YnXoX+B6M | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (2cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 37 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|