ScreenShot
| Created | 2024.09.22 18:01 | Machine | s1_win7_x6403 |
| Filename | niceworkonudpationprocesstogetmebackwtihentirethingstobefineformetounderstandallgreatgoingtobethanksforevery_______nicepeoplesaround.doc | ||
| Type | Rich Text Format data, version 1, unknown character set | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 39 detected (Common, ObfsObjDat, obfuscated, Save, CVE-2017-1188, multiple detections, REMCOS, YXEINZ, Malicious, score, dinbqn, CLASSIC, pwiho, RtfExp, Detected, Camelot, Malform, RTFObfustream, Probably Heur, RTFObfuscation, Cwnw) | ||
| md5 | d63c7600ca42fe65af91ae662ef7b637 | ||
| sha256 | eb0786d23a2ada26a937a41d56a96514a3df0027ff857d0407d462adfba18ddb | ||
| ssdeep | 384:vnHdoOarkwlJbmbKLY17V/W7ZftG5eqVdwRQb65Y2zdfGxswDRa:vnHmOarkwTzs174geqVCFux7a | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (10cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 39 AntiVirus engines on VirusTotal as malicious |
| watch | Communicates with host for which no DNS query was performed |
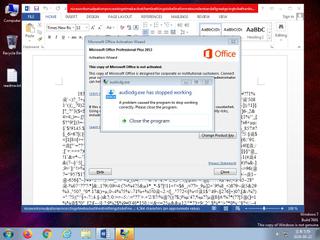
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates (office) documents on the filesystem |
| notice | Creates hidden or system file |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | RTF file has an unknown character set |
| info | One or more processes crashed |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | SUSP_INDICATOR_RTF_MalVer_Objects | Detects RTF documents with non-standard version and embedding one of the object mostly observed in exploit (e.g. CVE-2017-11882) documents. | binaries (upload) |
| info | Rich_Text_Format_Zero | Rich Text Format Signature Zero | binaries (upload) |
Network (4cnts) ?
Suricata ids
ET INFO Executable Download from dotted-quad Host
ET MALWARE Likely Evil EXE download from dotted Quad by MSXMLHTTP M1
ET POLICY PE EXE or DLL Windows file download HTTP
ET MALWARE Likely Evil EXE download from dotted Quad by MSXMLHTTP M2
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
SURICATA TLS invalid record type
SURICATA TLS invalid record/traffic
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET MALWARE Likely Evil EXE download from dotted Quad by MSXMLHTTP M1
ET POLICY PE EXE or DLL Windows file download HTTP
ET MALWARE Likely Evil EXE download from dotted Quad by MSXMLHTTP M2
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
SURICATA TLS invalid record type
SURICATA TLS invalid record/traffic
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)