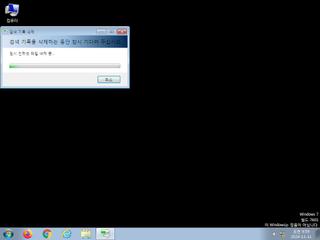
ScreenShot
| Created | 2024.11.11 10:31 | Machine | s1_win7_x6401 |
| Filename | bxn.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | |||
| VT API (file) | 50 detected (AIDetectMalware, Malicious, score, Occamy, Infected, GenericKD, Unsafe, confidence, 100%, Attribute, HighConfidence, moderate confidence, NewHeur, Razy, gwfsre, CLOUD, dpmsk, DownLoader32, 0NA103FE24, Detected, AGeneric, HeurC, KVM006, Malware@#3ejqz7cp0yi2f, Artemis, GdSda, Small, susgen, PossibleThreat) | ||
| md5 | 63399c74c5dda6fa8276ded35b5118b9 | ||
| sha256 | d121605217cfec4a341b4b889ec374d6bc0be6b93886e4a6788865f9022be50a | ||
| ssdeep | 768:P45UMrFV1yQlNBqHpBtzs2N77F/WTI+owQ:UJrFV1yQlzqztzsJo | ||
| imphash | fb7c144ac94c7da0fce62e3df10c5951 | ||
| impfuzzy | 48:nmOz/wzwgmlcwbnlgkRJ13ucZyworW3esm3Fyp9FNme4zpc9lwPs7gkSIW9IXBZ2:nmOz/GfmlculgkRJ1+codrWuL1yp9FNe | ||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 50 AntiVirus engines on VirusTotal as malicious |
| watch | Deletes a large number of files from the system indicative of ransomware |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Drops an executable to the user AppData folder |
| notice | Foreign language identified in PE resource |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | One or more processes crashed |
Rules (14cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | HermeticWiper_Zero | HermeticWiper | binaries (download) |
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | Javascript_Blob | use blob(Binary Large Objec) javascript | binaries (download) |
| info | icon_file_format | icon file format | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | JPEG_Format_Zero | JPEG Format | binaries (download) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | PNG_Format_Zero | PNG Format | binaries (download) |
PE API
IAT(Import Address Table) Library
MSVBVM60.DLL
0x401000 __vbaVarTstGt
0x401004 __vbaStrI2
0x401008 _CIcos
0x40100c _adj_fptan
0x401010 __vbaVarMove
0x401014 __vbaFreeVar
0x401018 __vbaFreeVarList
0x40101c __vbaEnd
0x401020 _adj_fdiv_m64
0x401024 __vbaNextEachVar
0x401028 __vbaFreeObjList
0x40102c __vbaLineInputVar
0x401030 _adj_fprem1
0x401034 None
0x401038 __vbaStrCat
0x40103c __vbaSetSystemError
0x401040 __vbaHresultCheckObj
0x401044 _adj_fdiv_m32
0x401048 __vbaExitProc
0x40104c __vbaObjSet
0x401050 __vbaOnError
0x401054 _adj_fdiv_m16i
0x401058 _adj_fdivr_m16i
0x40105c None
0x401060 __vbaFPFix
0x401064 __vbaBoolVarNull
0x401068 _CIsin
0x40106c __vbaChkstk
0x401070 __vbaFileClose
0x401074 EVENT_SINK_AddRef
0x401078 None
0x40107c None
0x401080 __vbaObjVar
0x401084 DllFunctionCall
0x401088 _adj_fpatan
0x40108c __vbaStrR8
0x401090 EVENT_SINK_Release
0x401094 None
0x401098 _CIsqrt
0x40109c __vbaObjIs
0x4010a0 EVENT_SINK_QueryInterface
0x4010a4 __vbaExceptHandler
0x4010a8 __vbaPrintFile
0x4010ac _adj_fprem
0x4010b0 _adj_fdivr_m64
0x4010b4 None
0x4010b8 None
0x4010bc __vbaFPException
0x4010c0 __vbaInStrVar
0x4010c4 __vbaVarCat
0x4010c8 _CIlog
0x4010cc __vbaErrorOverflow
0x4010d0 __vbaFileOpen
0x4010d4 __vbaR8Str
0x4010d8 __vbaVarLateMemCallLdRf
0x4010dc __vbaNew2
0x4010e0 _adj_fdiv_m32i
0x4010e4 _adj_fdivr_m32i
0x4010e8 __vbaFreeStrList
0x4010ec _adj_fdivr_m32
0x4010f0 _adj_fdiv_r
0x4010f4 None
0x4010f8 None
0x4010fc __vbaVarTstNe
0x401100 __vbaVarSetVar
0x401104 __vbaLateMemCall
0x401108 __vbaVarDup
0x40110c __vbaStrToAnsi
0x401110 __vbaFpI4
0x401114 __vbaVarLateMemCallLd
0x401118 __vbaUnkVar
0x40111c __vbaVarCopy
0x401120 __vbaVarSetObjAddref
0x401124 _CIatan
0x401128 __vbaStrMove
0x40112c __vbaForEachVar
0x401130 None
0x401134 _allmul
0x401138 _CItan
0x40113c None
0x401140 __vbaAryUnlock
0x401144 _CIexp
0x401148 __vbaFreeObj
0x40114c __vbaFreeStr
EAT(Export Address Table) is none
MSVBVM60.DLL
0x401000 __vbaVarTstGt
0x401004 __vbaStrI2
0x401008 _CIcos
0x40100c _adj_fptan
0x401010 __vbaVarMove
0x401014 __vbaFreeVar
0x401018 __vbaFreeVarList
0x40101c __vbaEnd
0x401020 _adj_fdiv_m64
0x401024 __vbaNextEachVar
0x401028 __vbaFreeObjList
0x40102c __vbaLineInputVar
0x401030 _adj_fprem1
0x401034 None
0x401038 __vbaStrCat
0x40103c __vbaSetSystemError
0x401040 __vbaHresultCheckObj
0x401044 _adj_fdiv_m32
0x401048 __vbaExitProc
0x40104c __vbaObjSet
0x401050 __vbaOnError
0x401054 _adj_fdiv_m16i
0x401058 _adj_fdivr_m16i
0x40105c None
0x401060 __vbaFPFix
0x401064 __vbaBoolVarNull
0x401068 _CIsin
0x40106c __vbaChkstk
0x401070 __vbaFileClose
0x401074 EVENT_SINK_AddRef
0x401078 None
0x40107c None
0x401080 __vbaObjVar
0x401084 DllFunctionCall
0x401088 _adj_fpatan
0x40108c __vbaStrR8
0x401090 EVENT_SINK_Release
0x401094 None
0x401098 _CIsqrt
0x40109c __vbaObjIs
0x4010a0 EVENT_SINK_QueryInterface
0x4010a4 __vbaExceptHandler
0x4010a8 __vbaPrintFile
0x4010ac _adj_fprem
0x4010b0 _adj_fdivr_m64
0x4010b4 None
0x4010b8 None
0x4010bc __vbaFPException
0x4010c0 __vbaInStrVar
0x4010c4 __vbaVarCat
0x4010c8 _CIlog
0x4010cc __vbaErrorOverflow
0x4010d0 __vbaFileOpen
0x4010d4 __vbaR8Str
0x4010d8 __vbaVarLateMemCallLdRf
0x4010dc __vbaNew2
0x4010e0 _adj_fdiv_m32i
0x4010e4 _adj_fdivr_m32i
0x4010e8 __vbaFreeStrList
0x4010ec _adj_fdivr_m32
0x4010f0 _adj_fdiv_r
0x4010f4 None
0x4010f8 None
0x4010fc __vbaVarTstNe
0x401100 __vbaVarSetVar
0x401104 __vbaLateMemCall
0x401108 __vbaVarDup
0x40110c __vbaStrToAnsi
0x401110 __vbaFpI4
0x401114 __vbaVarLateMemCallLd
0x401118 __vbaUnkVar
0x40111c __vbaVarCopy
0x401120 __vbaVarSetObjAddref
0x401124 _CIatan
0x401128 __vbaStrMove
0x40112c __vbaForEachVar
0x401130 None
0x401134 _allmul
0x401138 _CItan
0x40113c None
0x401140 __vbaAryUnlock
0x401144 _CIexp
0x401148 __vbaFreeObj
0x40114c __vbaFreeStr
EAT(Export Address Table) is none