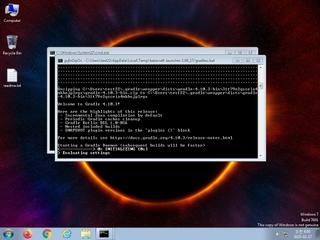
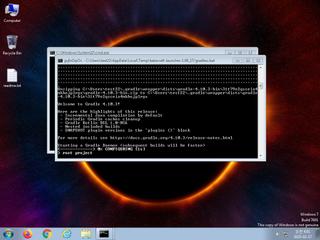
ScreenShot
| Created | 2025.02.18 18:16 | Machine | s1_win7_x6403_us |
| Filename | gradlew.bat | ||
| Type | ASCII text, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 632f7f6dcc28a13f168cc431061e0438 | ||
| sha256 | 398db6d288bcbfc7b2059f15e2bb6f301cb39e8c421bd1e5c5682ab9bb8ed104 | ||
| ssdeep | 48:YmdmK63w2StxW2WK0N2gjPWK0mKMdCe3duCmKfzfbzx1:YmYpSGaPCP | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| watch | Appends a known multi-family ransomware file extension to files that have been encrypted |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | One or more potentially interesting buffers were extracted |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Starts servers listening |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Command line console output was observed |
| info | One or more processes crashed |
Rules (42cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Network_Downloader | File Downloader | memory |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PNG_Format_Zero | PNG Format | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
| info | zip_file_format | ZIP file format | binaries (download) |