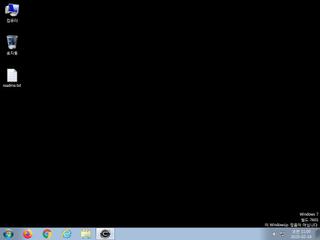
ScreenShot
| Created | 2025.02.19 11:07 | Machine | s1_win7_x6401 |
| Filename | cabal.exe | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | |||
| VT API (file) | |||
| md5 | c0b915db483249fbb011d4c73d0dbf1f | ||
| sha256 | 1e997ac3340205e49c67004ba0d78f67e4696eaaecaa239e6aa8bdb357496ab9 | ||
| ssdeep | 1536:1jOHRPqUVgGanX+DFVZHJqtBy3dbEKshUtjG9X4n4PZHJqtBy3dbTZH1ttBc3dbj:gRTV9uX+/tktGn8cGVtktGZtXt4d | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (22cnts)
| Level | Description |
|---|---|
| warning | Generates some ICMP traffic |
| watch | Appends a known multi-family ransomware file extension to files that have been encrypted |
| watch | Communicates with host for which no DNS query was performed |
| watch | Drops 107 unknown file mime types indicative of ransomware writing encrypted files back to disk |
| watch | Looks for the Windows Idle Time to determine the uptime |
| watch | One or more of the buffers contains an embedded PE file |
| notice | A process attempted to delay the analysis task. |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An executable file was downloaded by the processes cabal.exe |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Terminates another process |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | This executable has a PDB path |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (21cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Emotet_2_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Network_Downloader | File Downloader | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (download) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (upload) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| info | CAB_file_format | CAB archive file | binaries (download) |
| info | Is_DotNET_DLL | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (118cnts) ?
Suricata ids
ET INFO Executable Download from dotted-quad Host
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET INFO Dotted Quad Host DLL Request
ET INFO Packed Executable Download
ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging)
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET INFO Dotted Quad Host DLL Request
ET INFO Packed Executable Download
ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging)
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none