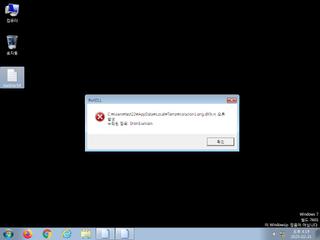
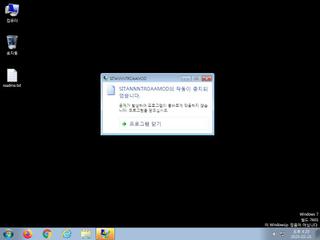
ScreenShot
| Created | 2025.02.21 16:23 | Machine | s1_win7_x6401 |
| Filename | coracion1.png | ||
| Type | PE32+ executable (DLL) (console) x86-64 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 37 detected (BXRat, Unsafe, malicious, confidence, GenericKD, high confidence, BackdoorX, cknpn, Static AI, Malicious PE, Detected, Phonzy, W0PYC0, ABBackdoor, SWDS, Artemis, Chgt, Anhl) | ||
| md5 | 33b528941a4932848cb9471b75d1a500 | ||
| sha256 | 460a5728b2fcff19f35cf34b671b61e6f9946ab698b5149704793c6c0d41fffb | ||
| ssdeep | 12288:fbauxPRWgCULYc4y9OP4lgFZThRKq7vwffH+3LB/P3+:fuEYRULp1OwlGxeyw3H+RP3+ | ||
| imphash | dae02f32a21e03ce65412f6e56942daa | ||
| impfuzzy | 3:rGsKZK:2Y | ||
Network IP location
Signature (12cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 37 AntiVirus engines on VirusTotal as malicious |
| watch | Communicates with host for which no DNS query was performed |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (6cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | Is_DotNET_DLL | (no description) | binaries (upload) |
| info | IsDLL | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorDllMain
EAT(Export Address Table) Library
0x4b16d2 RHBinder__ShimExeMain
0x4b16e2 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDF
0x4b1772 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDMM
0x4b1782 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDMMNH
0x4b1792 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDMRRRTTT
0x4b1742 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPCF
0x4b1712 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPJ
0x4b1702 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPR
0x4b1752 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPRS
0x4b1732 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPSS
0x4b1722 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPT
0x4b1762 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDVV
0x4b16f2 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDX
mscoree.dll
0x402000 _CorDllMain
EAT(Export Address Table) Library
0x4b16d2 RHBinder__ShimExeMain
0x4b16e2 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDF
0x4b1772 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDMM
0x4b1782 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDMMNH
0x4b1792 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDMRRRTTT
0x4b1742 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPCF
0x4b1712 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPJ
0x4b1702 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPR
0x4b1752 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPRS
0x4b1732 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPSS
0x4b1722 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDPT
0x4b1762 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDVV
0x4b16f2 qnEKZxaVxYGRvkuUprJLCoeoZnHEWnTtYMhweGUKDX