| Created | 2025.03.13 09:58 | Machine | s1_win7_x6401 |
| Filename | brain.ps1 | ||
| Type | ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 14 detected (Countermeasure, DotNetToJScript, Attribute, HighConfidence, PowerShell, POWLOAD, SMERB, Zapchast, MulDrop, PSDrop, Detected, Boxter, HNBE, Encpe) | ||
| md5 | 62f57d817459bd722949f54a03302b88 | ||
| sha256 | 5a07f8d776d28bf2ce80615f558d4002be4f19e6f9b35ff7aec76d963a2891f9 | ||
| ssdeep | 1536:Ea8QOgLzmKoJo9bcnvKjCcaI+iFodWo02wjx:ZbCK9bcnvKjCcaI+iFodWo1wjx | ||
| imphash | |||
| impfuzzy | |||
Network IP location


























Signature (26cnts)
| Level | Description |
|---|---|
| danger | The process powershell.exe wrote an executable file to disk which it then attempted to execute |
| danger | Executed a process and injected code into it |
| watch | A process performed obfuscation on information about the computer or sent it to a remote location indicative of CnC Traffic/Preperations. |
| watch | Allocates execute permission to another process indicative of possible code injection |
| watch | Code injection by writing an executable or DLL to the memory of another process |
| watch | Communicates with host for which no DNS query was performed |
| watch | Creates a windows hook that monitors keyboard input (keylogger) |
| watch | Drops a binary and executes it |
| watch | File has been identified by 14 AntiVirus engines on VirusTotal as malicious |
| watch | One or more non-whitelisted processes were created |
| watch | Potential code injection by writing to the memory of another process |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | Used NtSetContextThread to modify a thread in a remote process indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | Drops an executable to the user AppData folder |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
Rules (24cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win_Trojan_Formbook_Zero | Used Formbook | binaries (upload) |
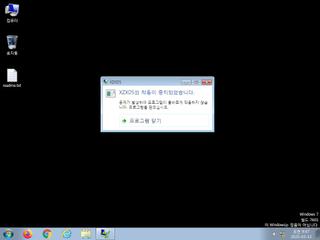
| danger | Win_XWorm_3_M_Zero | Win XWorm V3.1 | memory |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | hide_executable_file | Hide executable file | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | ConfuserEx_Zero | Confuser .NET | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | RAT_WebCam | Remote Administration toolkit using webcam | memory |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | Is_DotNET_DLL | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
Suricata ids
ET INFO Executable Download from dotted-quad Host
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response