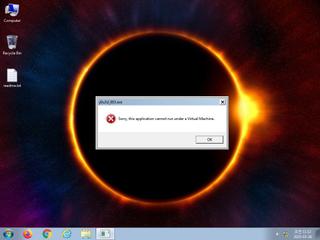
ScreenShot
| Created | 2025.03.26 11:25 | Machine | s1_win7_x6403 |
| Filename | y0u3d_003.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
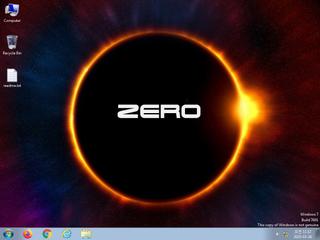
| ZERO API | |||
| VT API (file) | 55 detected (AIDetectMalware, BypassUAC, Malicious, score, Ghanarava, nD0@tOdDrWni, Unsafe, Vl8u, confidence, 100%, Genus, high confidence, VMProtect, BC suspicious, MalwareX, kwjnpx, LESS, bWQ1Oq0FJ06W3JE9ck7pxt, gx3o, XPACK, Inject5, AMADEY, YXFCXZ, high, Static AI, Malicious PE, Detected, Caynamer, ABTrojan, JMCI, R696482, Artemis, Nzfl, 8P91eGX0H40, susgen) | ||
| md5 | 398ab46e27982dfd2028bf42f4832fa8 | ||
| sha256 | 033d584799e9ce55c7fc62adb86a6738a42fe2fa5f21035b66ee7b6c4c1fd6e1 | ||
| ssdeep | 24576:6egwtp24lYhcvTvUFWuqZ3Gb4gVJC158EsEYaQrQsJILVm9biGkbQjI/z:QQLl/442bYn9nY8mEGkb | ||
| imphash | 55347c971789434361ebf2c1c21a714b | ||
| impfuzzy | 3:sy8E47HGXGRr74wKWbsKnqMEleA+n:UEGgGv4wNbsKn3EQn | ||
Network IP location
Signature (3cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 55 AntiVirus engines on VirusTotal as malicious |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) Library
KERNEL32.dll
0x549000 OpenMutexW
USER32.dll
0x549008 wsprintfW
ole32.dll
0x549010 CoCreateInstance
OLEAUT32.dll
0x549018 VariantClear
EAT(Export Address Table) Library
0x405ab0 GetModuleHandle64
0x406080 GetProcAddress64
0x406680 GetThreadContext64
0x4064a0 ReadProcessMemory64
0x406000 SetLastErrorFromX64Call
0x406730 SetThreadContext64
0x406220 VirtualAllocEx64
0x406300 VirtualFreeEx64
0x4063d0 VirtualProtectEx64
0x406150 VirtualQueryEx64
0x406590 WriteProcessMemory64
0x405740 X64Call
KERNEL32.dll
0x549000 OpenMutexW
USER32.dll
0x549008 wsprintfW
ole32.dll
0x549010 CoCreateInstance
OLEAUT32.dll
0x549018 VariantClear
EAT(Export Address Table) Library
0x405ab0 GetModuleHandle64
0x406080 GetProcAddress64
0x406680 GetThreadContext64
0x4064a0 ReadProcessMemory64
0x406000 SetLastErrorFromX64Call
0x406730 SetThreadContext64
0x406220 VirtualAllocEx64
0x406300 VirtualFreeEx64
0x4063d0 VirtualProtectEx64
0x406150 VirtualQueryEx64
0x406590 WriteProcessMemory64
0x405740 X64Call