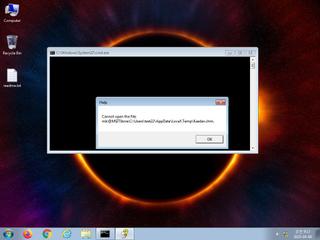
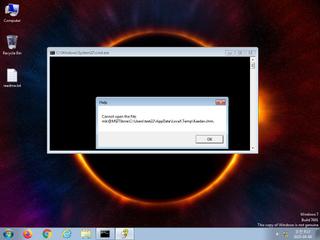
ScreenShot
| Created | 2025.04.08 09:17 | Machine | s1_win7_x6403 |
| Filename | Kaeder.chm | ||
| Type | ASCII text, with very long lines, with no line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | |||
| md5 | aa6bdcff75c2a7f82ffd2c6b53e2d5b3 | ||
| sha256 | d1786eebab7680732ea0e19b552c0b1de308ebab47e5373a05d1ad3af0148693 | ||
| ssdeep | 12288:ql3dFPCVVw0Eiw432yr3Huj0ddoUKpjPwZZ8vYWc0EOfEYV5x:qlNpCVVw5y7uj0ddypjA/Wc/wEYp | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (4cnts)
| Level | Description |
|---|---|
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | One or more processes crashed |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Suspicious_Obfuscation_Script_2 | Suspicious obfuscation script (e.g. executable files) | binaries (upload) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|