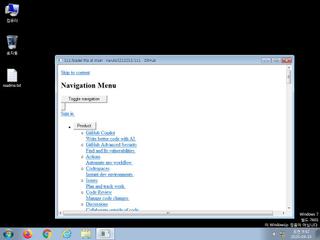
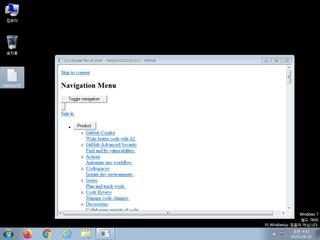
ScreenShot
| Created | 2025.04.15 09:45 | Machine | s1_win7_x6401 |
| Filename | loader.hta | ||
| Type | HTML document, UTF-8 Unicode text, with very long lines | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 3d38ab222579d17632acd5d383490a05 | ||
| sha256 | 7ac6f0e34ab766fbb5b199db456aa924bee38561da2d6ea18afd82cdcab06bd2 | ||
| ssdeep | 6144:bTsrzp8c/saqk3V97HILqgIDSF5Ig9bvZJT3CqbMrhryf65NRPaCieMjAkvCJv1P:3srzp8c/saqk3V97HILqgIDSF5Ig9bvA | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (4cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| info | Checks amount of memory in system |
Rules (0cnts)
| Level | Name | Description | Collection |
|---|
Suricata ids
ET DROP Spamhaus DROP Listed Traffic Inbound group 13
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)