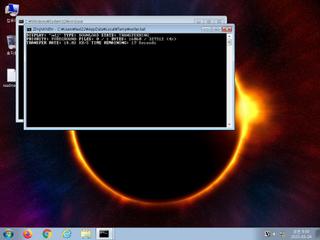
ScreenShot
| Created | 2023.03.24 09:45 | Machine | s1_win7_x6402 |
| Filename | writer.bat | ||
| Type | UTF-8 Unicode (with BOM) text, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 1e30daa4770b00c2e624e8a615e80282 | ||
| sha256 | 642261ea81f01257944208fd7581532fad55c3133ca418ceb7b8c17fc7002ad6 | ||
| ssdeep | 24:24yBR4yBD4yBV4yBf4yBd4yBaB7RRBWD7S:2JRJDJVJfJdJinj | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| danger | Connects to IP addresses that are no longer responding to requests (legitimate services will remain up-and-running usually) |
| watch | BITSAdmin Tool has been invoked to download a file |
| watch | Connects to an IRC server |
| watch | Uses suspicious command line tools or Windows utilities |
| notice | Connects to a Dynamic DNS Domain |
| notice | Created a process named as a common system process |
| notice | Creates a suspicious process |
| notice | Performs some HTTP requests |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Command line console output was observed |
Rules (31cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Network_Downloader | File Downloader | memory |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
Network (8cnts) ?
Suricata ids
ET POLICY DNS Query to DynDNS Domain *.ddns .net
ET INFO DYNAMIC_DNS HTTP Request to a *.ddns .net Domain
ET INFO PS1 Powershell File Request
ET HUNTING Generic Powershell Launching Hidden Window
ET HUNTING Suspicious svchost.exe in URI - Possible Process Dump/Trojan Download
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO DYNAMIC_DNS HTTP Request to a *.ddns .net Domain
ET INFO PS1 Powershell File Request
ET HUNTING Generic Powershell Launching Hidden Window
ET HUNTING Suspicious svchost.exe in URI - Possible Process Dump/Trojan Download
ET POLICY PE EXE or DLL Windows file download HTTP