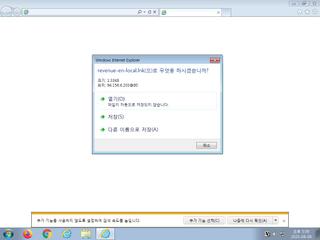
ScreenShot
| Created | 2023.08.09 17:13 | Machine | s1_win7_x6402 |
| Filename | en-win-upd(localchr).url | ||
| Type | MS Windows 95 Internet shortcut text (URL= |
||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | |||
| VT API (file) | |||
| md5 | f8bf0dddb23f80f69552a2fb661393b5 | ||
| sha256 | 87a2454abaea25f30348e0662010cc32789ca71faf0151c5f0e151fba6859894 | ||
| ssdeep | 3:HRAbABGQYmimiLXIhzKEgOMGHJdEPUo1YSo/QJ5eQvyYesbBSn:HRYFVmizLXczfX5JAISoIJ5eQvyYesbw | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (17cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| watch | The process powershell.exe wrote an executable file to disk |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (8cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |