ScreenShot
| Created | 2023.08.24 09:23 | Machine | s1_win7_x6401 |
| Filename | d9e1c3_337d702a7383407ea927e15f24052b8b.txt.ps1 | ||
| Type | ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 2 detected () | ||
| md5 | 10c83f5b34882b38cfcde8064af6c34b | ||
| sha256 | 0b9f41f810ef6352e7ecb6441af26f60a43d98a49aeee939a5935fda03380296 | ||
| ssdeep | 384:0WnPZ/WxrZtbKH8iUumsWn/3sIy/UvIa7pUO820QkeXFfcRK63CPjTOkKJ3wjWv0:tV+pU7nS | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (13cnts)
| Level | Description |
|---|---|
| watch | A potential heapspray has been detected. 115 megabytes was sprayed onto the heap of the powershell.exe process |
| watch | Installs itself for autorun at Windows startup |
| watch | One or more non-whitelisted processes were created |
| watch | The process powershell.exe wrote an executable file to disk |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | File has been identified by 2 AntiVirus engines on VirusTotal as malicious |
| notice | Uses Windows utilities for basic Windows functionality |
| info | Checks amount of memory in system |
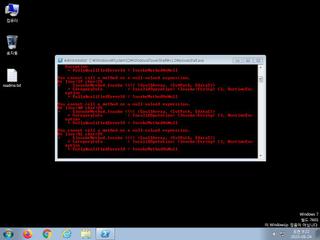
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|