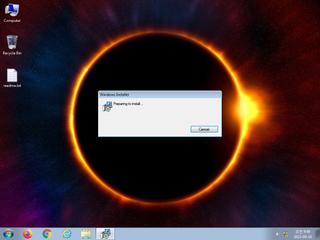
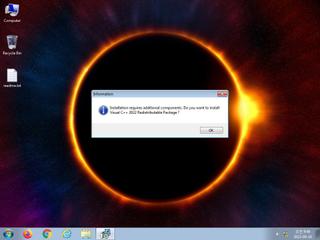
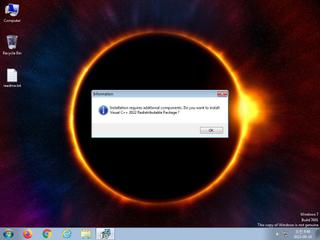
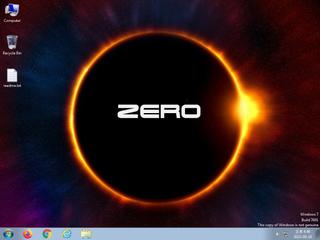
ScreenShot
| Created | 2023.09.18 09:48 | Machine | s1_win7_x6403 |
| Filename | forex.msi | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 14:06:51 2020, Security: 0, Code page: 1252, Revision Number: {887DC08E-7563-4B0B-B863-2 | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 6 detected (LUMMASTEALER, YXDIJZ, Artemis, ILCrypt, Detected, PossibleThreat) | ||
| md5 | 452db598b23ac2a6cd0d4d4692f1c438 | ||
| sha256 | 396eedecaf60b2cf33e4b54f7eff42ab1d92c26ca9c81f2d1eb0323ca100f737 | ||
| ssdeep | 393216:qohwo064S07VmAEBr2KmWd84QLYDIUc5b29UUENsIJ:Xwo0wAEr2LWi4v3GbCUxsI | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (13cnts)
| Level | Description |
|---|---|
| watch | Attempts to create or modify system certificates |
| watch | One or more of the buffers contains an embedded PE file |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | File has been identified by 6 AntiVirus engines on VirusTotal as malicious |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | One or more potentially interesting buffers were extracted |
| notice | Performs some HTTP requests |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | Sends data using the HTTP POST Method |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
Rules (5cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| info | CAB_file_format | CAB archive file | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
Suricata ids
ET MALWARE [ANY.RUN] Win32/Lumma Stealer Configuration Request Attempt
ET INFO Unconfigured nginx Access
ET INFO Unconfigured nginx Access