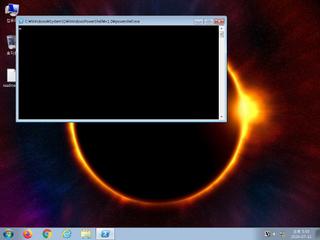
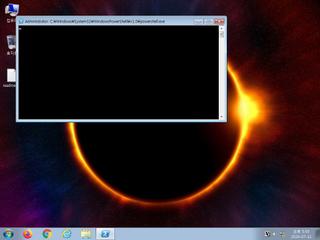
ScreenShot
| Created | 2024.07.11 17:48 | Machine | s1_win7_x6402 |
| Filename | reg.jpg.vbs | ||
| Type | UTF-8 Unicode text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 22 detected (GenericKD, a variant of Generik, DCMMTQW, ASYNCRAT, YXEFXZ, Undefined, TOPIS, fPZYvCxD07, PowerShell, Detected, Casdet, ABTrojan, QPYO, ai score=88, Unknow) | ||
| md5 | ed5c34496df2011a496b53abc7034a0d | ||
| sha256 | 1d1126c994761ec652e9b49a7c028545dc3d381cc49163ab45cece7be31ea793 | ||
| ssdeep | 3072:m9KqylccWmDwZmT8VjG3/Dyqr4cwt9aU0ruzjzuJmmwc0/Kz0o+i/6n/cGyjBhKh:z+26xhfptqUk84LnO5mH9OdHUb3ngoI | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (9cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 22 AntiVirus engines on VirusTotal as malicious |
| watch | Installs itself for autorun at Windows startup |
| watch | Stores PowerShell commands in the registry likely for persistence |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates executable files on the filesystem |
| info | Checks amount of memory in system |
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (3cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|