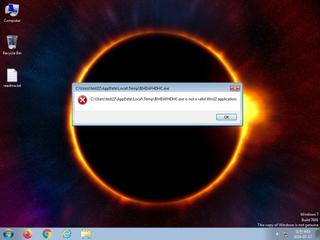
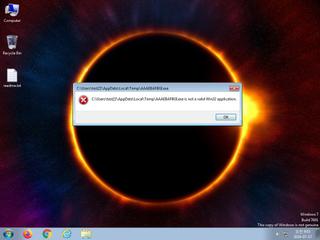
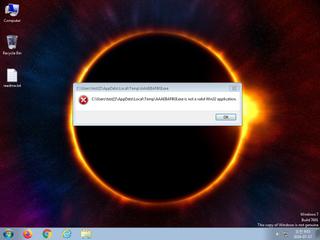
ScreenShot
| Created | 2024.07.17 09:06 | Machine | s1_win7_x6403 |
| Filename | chart.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 39 detected (AIDetectMalware, malicious, high confidence, score, Unsafe, Vron, Attribute, HighConfidence, EnigmaProtector, J suspicious, Artemis, PWSX, Stealc, AGEN, Real Protect, high, Detected, StealerC, HeurC, KVMH008, ZexaF, fzW@aKqGF5n, BScope, Probably Heur, ExeHeaderL, Static AI, Malicious PE, susgen, confidence, 100%, GMH2XJC) | ||
| md5 | 73aa6448467db3d1ac25f7e9d8cf1cd4 | ||
| sha256 | 931076586d551cccba6532aeb6393cc64ab293035c582125ef32e7eb82e3b0e5 | ||
| ssdeep | 24576:tUFuDtv4dsn0Ff5qI/z8L642KlCWZr9zs7wKztmZ7RGP3Wg+8o:tvDtvnn0R5h3cLZ9smNR0W4o | ||
| imphash | 001806c33a6e9fe5fbff34bdbd79b591 | ||
| impfuzzy | 6:nERGDvZ/OiBJAEcXQwDLzRgSdn8BbMqtYbdb2n:EcDvZGqA9AwDXRgKQcb2n | ||
Network IP location
Signature (27cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| danger | File has been identified by 39 AntiVirus engines on VirusTotal as malicious |
| watch | Checks the CPU name from registry |
| watch | Collects information about installed applications |
| watch | Communicates with host for which no DNS query was performed |
| watch | Harvests credentials from local email clients |
| watch | Harvests credentials from local FTP client softwares |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An executable file was downloaded by the process chart.exe |
| notice | Creates a suspicious process |
| notice | Creates executable files on the filesystem |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Queries for potentially installed applications |
| notice | Searches running processes potentially to identify processes for sandbox evasion |
| notice | Sends data using the HTTP POST Method |
| notice | Steals private information from local Internet browsers |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Command line console output was observed |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | The executable contains unknown PE section names indicative of a packer (could be a false positive) |
| info | Tries to locate where the browsers are installed |
Rules (20cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Packer_Zero | Malicious Packer | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (10cnts) ?
Suricata ids
ET DROP Spamhaus DROP Listed Traffic Inbound group 9
ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in
ET MALWARE Win32/Stealc Requesting browsers Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with browsers Config M1
ET MALWARE Win32/Stealc Requesting plugins Config from C2
ET INFO Dotted Quad Host DLL Request
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET MALWARE Win32/Stealc/Vidar Stealer Active C2 Responding with plugins Config M1
ET MALWARE Win32/Stealc Submitting System Information to C2
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
ET MALWARE [SEKOIA.IO] Win32/Stealc C2 Check-in
ET MALWARE Win32/Stealc Requesting browsers Config from C2
ET MALWARE Win32/Stealc Active C2 Responding with browsers Config M1
ET MALWARE Win32/Stealc Requesting plugins Config from C2
ET INFO Dotted Quad Host DLL Request
ET HUNTING HTTP GET Request for freebl3.dll - Possible Infostealer Activity
ET MALWARE Win32/Stealc/Vidar Stealer Active C2 Responding with plugins Config M1
ET MALWARE Win32/Stealc Submitting System Information to C2
ET HUNTING HTTP GET Request for sqlite3.dll - Possible Infostealer Activity
ET POLICY PE EXE or DLL Windows file download HTTP
ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download
ET HUNTING HTTP GET Request for mozglue.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for nss3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for softokn3.dll - Possible Infostealer Activity
ET HUNTING HTTP GET Request for vcruntime140.dll - Possible Infostealer Activity
PE API
IAT(Import Address Table) Library
kernel32.dll
0x8ba0d4 GetModuleHandleA
0x8ba0d8 GetProcAddress
0x8ba0dc ExitProcess
0x8ba0e0 LoadLibraryA
user32.dll
0x8ba0e8 MessageBoxA
advapi32.dll
0x8ba0f0 RegCloseKey
oleaut32.dll
0x8ba0f8 SysFreeString
gdi32.dll
0x8ba100 CreateFontA
shell32.dll
0x8ba108 ShellExecuteA
version.dll
0x8ba110 GetFileVersionInfoA
msvcrt.dll
0x8ba118 strncpy
EAT(Export Address Table) is none
kernel32.dll
0x8ba0d4 GetModuleHandleA
0x8ba0d8 GetProcAddress
0x8ba0dc ExitProcess
0x8ba0e0 LoadLibraryA
user32.dll
0x8ba0e8 MessageBoxA
advapi32.dll
0x8ba0f0 RegCloseKey
oleaut32.dll
0x8ba0f8 SysFreeString
gdi32.dll
0x8ba100 CreateFontA
shell32.dll
0x8ba108 ShellExecuteA
version.dll
0x8ba110 GetFileVersionInfoA
msvcrt.dll
0x8ba118 strncpy
EAT(Export Address Table) is none