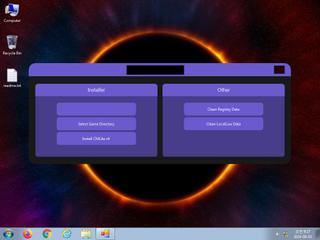
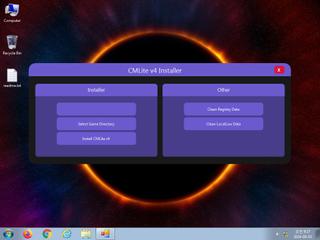
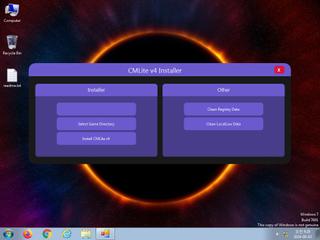
ScreenShot
| Created | 2024.09.03 09:36 | Machine | s1_win7_x6403 |
| Filename | CMLiteInstaller.exe | ||
| Type | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 26 detected (AIDetectMalware, Znyonm, malicious, moderate confidence, Unsafe, V0h9, Detected, Uwamson, RedLineStealer, Chgt, R002H01CF24, PossibleThreat) | ||
| md5 | 02ea34533272f916fb52990a45917913 | ||
| sha256 | 6dd45a770648da5f5996ac7b28f604493b44f8b1ba7458cf60d3a1ab7cf18590 | ||
| ssdeep | 24576:2xDVAu0gy5oaV/lEVSL24t4rmbe3Bw5m9YvWcdyFoBkkAxqV:2xDGu0gymI6kL14rmbCmU8xYan | ||
| imphash | |||
| impfuzzy | 3:: | ||
Network IP location
Signature (8cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 26 AntiVirus engines on VirusTotal as malicious |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
| info | This executable has a PDB path |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (4cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
PE API
IAT(Import Address Table) is none
EAT(Export Address Table) is none
EAT(Export Address Table) is none