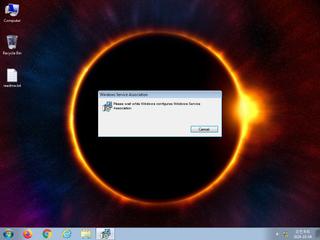
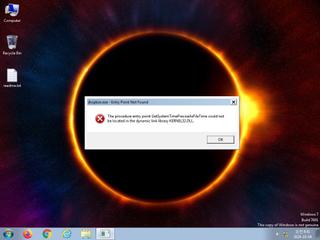
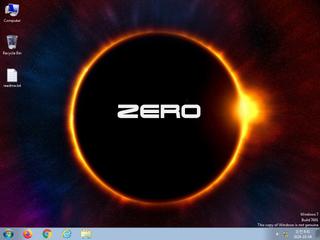
ScreenShot
| Created | 2024.10.04 08:46 | Machine | s1_win7_x6403 |
| Filename | BANDICUT.msi | ||
| Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 14:06:51 2020, Security: 0, Code page: 1252, | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 27 detected (Deyma, Malicious, score, Artemis, AGVN, MalwareX, vhtts, Amadey, Detected, pjokf, Wacatac, Agent5, Ymhl) | ||
| md5 | 087d510f4d69f6faa479e4919f51a175 | ||
| sha256 | 1dd7892458eab123c341452aff6f4d817f290efc7f8c97b76bdb78e1e1fcf8d2 | ||
| ssdeep | 98304:zYlRGJAeTgvVgl4GVRtc6gMwt9HQTFdoVXI0+S:k28gjzngPtFGe9W | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (10cnts)
| Level | Description |
|---|---|
| warning | File has been identified by 27 AntiVirus engines on VirusTotal as malicious |
| watch | Attempts to create or modify system certificates |
| watch | One or more of the buffers contains an embedded PE file |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | One or more potentially interesting buffers were extracted |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
Rules (6cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| info | CAB_file_format | CAB archive file | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|