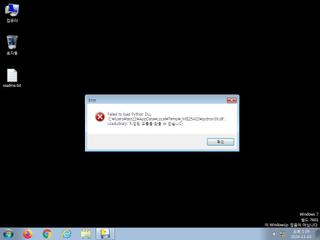
ScreenShot
| Created | 2024.11.03 13:44 | Machine | s1_win7_x6401 |
| Filename | DocTromTinNhan.exe | ||
| Type | PE32+ executable (GUI) x86-64, for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 32 detected (, HEUR:Trojan-PSW.Python.Agent.gen, Malicious, Trojan.Python.Psw, Detected, ti!82FE9FEA0B70, Infostealer.Python.Agent.V5lg, Win64:Malware-gen, Malicious (score: 99), exe.trojan.python, Artemis!25DD80DC8B9C, win/malicious_confidence_100% (D), BehavesLike.Win64.Agent.rc, Trojan.TR/AVI.Agent.dtfqq, Spyware.RedTiger, TrojanPSW:Win32/Almi_Stealer.c, MALICIOUS, Static AI - Suspicious PE, Trojan.PSW.Multi.oe, TR/AVI.Agent.dtfqq, Python/PSW.Agent.AZA, Trojan.Agent.Win32.3991781, Trojan.Win32.Python.i!c, generic.ml, Unsafe, Win32.Trojan-QQPass.QQRob.Gajl, W64.AIDetectMalware, Mal/Generic-S, PYC/Disgrab.D.gen!Camelot, TrojanSpy/Python.PwStealer.j) | ||
| md5 | 25dd80dc8b9c5e1afc5afb8c47253681 | ||
| sha256 | 82fe9fea0b7043c668a9bf291248035c3bdc75496ca0fbaf10be4e1e138a55a5 | ||
| ssdeep | 196608:giEk6XeI0H9onJ5hrZERoyiU8AdZYJERMEzsDyrTaup:BEk6n29c5hlER0AdZYy+0tr/ | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (6cnts)
| Level | Description |
|---|---|
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Creates executable files on the filesystem |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
Rules (49cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| danger | Win32_Trojan_Gen_1_0904B0_Zero | Win32 Trojan Emotet | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | ASPack_Zero | ASPack packed file | binaries (upload) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | Network_Downloader | File Downloader | memory |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| notice | anti_vm_detect | Possibly employs anti-virtualization techniques | binaries (download) |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | Persistence | Install itself for autorun at Windows startup | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE64 | (no description) | binaries (download) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |
| info | zip_file_format | ZIP file format | binaries (download) |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|