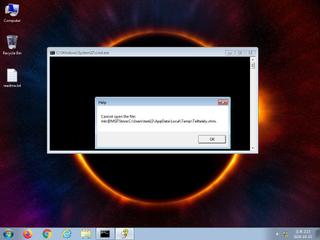
ScreenShot
| Created | 2024.10.15 14:18 | Machine | s1_win7_x6403 |
| Filename | Telltalely.chm | ||
| Type | ASCII text, with very long lines, with no line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 19a2f85327b3bca4544ea2a0880a5c5f | ||
| sha256 | 6b38ffe8bf309a42dd3702e1004209da0127c2ff43d69bcf9ef24fc35e0f3d87 | ||
| ssdeep | 6144:Uw6CCuFl4bHd6vOAhjT1dghhcUgNu71xjI0ieCuYm4VrEuw8PjiQOZrgoXFbow8G:XK9+ILC/zRhDiTxFGw8hV+SejAC/ | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (4cnts)
| Level | Description |
|---|---|
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | One or more processes crashed |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Suspicious_Obfuscation_Script_2 | Suspicious obfuscation script (e.g. executable files) | binaries (upload) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|