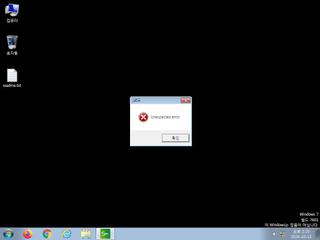
ScreenShot
| Created | 2024.10.15 14:33 | Machine | s1_win7_x6401 |
| Filename | update.exe | ||
| Type | PE32 executable (GUI) Intel 80386, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 49 detected (Common, Malicious, score, GenericKD, Unsafe, V7u2, confidence, 100%, VBGenus, Attribute, HighConfidence, MalwareX, kqsyqz, CLOUD, high, Static AI, Suspicious PE, GenKD, Detected, Phonzy, CSVN, Chgt, R03BH09FT24, Gencirc, susgen, PossibleThreat, PALLAS) | ||
| md5 | 340efe524c957a5c254f567c30b14b7d | ||
| sha256 | 1d8ad7a7f0b07b83f26162edda497eedc59071b880f379d0d382e174ec83c6af | ||
| ssdeep | 3072:aku32+azLpGGADxtpfgVsoHdBPYGG121RjF7GDzYlRg1+7nku32+azLpGGADxtpC:akuG+apADxjfgZox21RjF7G8lg+jkuG5 | ||
| imphash | c39234ff2245e05d4a92d8a0891a5638 | ||
| impfuzzy | 24:n9wwzBCfVgkyQlrj1JTy5SGFESFNtp8wfGsJTSwMSwC:nqwzIgkxrj1JTy0GzFNtp8w+sJTSwMSL | ||
Network IP location
Signature (6cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 49 AntiVirus engines on VirusTotal as malicious |
| watch | Communicates with host for which no DNS query was performed |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Foreign language identified in PE resource |
| info | Checks amount of memory in system |
Rules (6cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Admin_Tool_IN_Zero | Admin Tool Sysinternals | binaries (upload) |
| watch | Network_Downloader | File Downloader | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
PE API
IAT(Import Address Table) Library
MSVBVM60.DLL
0x401000 _CIcos
0x401004 _adj_fptan
0x401008 __vbaFreeVar
0x40100c __vbaEnd
0x401010 _adj_fdiv_m64
0x401014 _adj_fprem1
0x401018 __vbaStrCat
0x40101c __vbaSetSystemError
0x401020 __vbaHresultCheckObj
0x401024 _adj_fdiv_m32
0x401028 _adj_fdiv_m16i
0x40102c _adj_fdivr_m16i
0x401030 _CIsin
0x401034 __vbaChkstk
0x401038 __vbaFileClose
0x40103c EVENT_SINK_AddRef
0x401040 __vbaStrCmp
0x401044 DllFunctionCall
0x401048 _adj_fpatan
0x40104c EVENT_SINK_Release
0x401050 None
0x401054 _CIsqrt
0x401058 EVENT_SINK_QueryInterface
0x40105c __vbaExceptHandler
0x401060 __vbaInputFile
0x401064 __vbaStrToUnicode
0x401068 _adj_fprem
0x40106c _adj_fdivr_m64
0x401070 __vbaFPException
0x401074 None
0x401078 _CIlog
0x40107c __vbaFileOpen
0x401080 __vbaNew2
0x401084 None
0x401088 _adj_fdiv_m32i
0x40108c _adj_fdivr_m32i
0x401090 __vbaFreeStrList
0x401094 _adj_fdivr_m32
0x401098 _adj_fdiv_r
0x40109c None
0x4010a0 __vbaStrToAnsi
0x4010a4 _CIatan
0x4010a8 __vbaStrMove
0x4010ac _allmul
0x4010b0 _CItan
0x4010b4 _CIexp
0x4010b8 __vbaFreeObj
0x4010bc __vbaFreeStr
EAT(Export Address Table) is none
MSVBVM60.DLL
0x401000 _CIcos
0x401004 _adj_fptan
0x401008 __vbaFreeVar
0x40100c __vbaEnd
0x401010 _adj_fdiv_m64
0x401014 _adj_fprem1
0x401018 __vbaStrCat
0x40101c __vbaSetSystemError
0x401020 __vbaHresultCheckObj
0x401024 _adj_fdiv_m32
0x401028 _adj_fdiv_m16i
0x40102c _adj_fdivr_m16i
0x401030 _CIsin
0x401034 __vbaChkstk
0x401038 __vbaFileClose
0x40103c EVENT_SINK_AddRef
0x401040 __vbaStrCmp
0x401044 DllFunctionCall
0x401048 _adj_fpatan
0x40104c EVENT_SINK_Release
0x401050 None
0x401054 _CIsqrt
0x401058 EVENT_SINK_QueryInterface
0x40105c __vbaExceptHandler
0x401060 __vbaInputFile
0x401064 __vbaStrToUnicode
0x401068 _adj_fprem
0x40106c _adj_fdivr_m64
0x401070 __vbaFPException
0x401074 None
0x401078 _CIlog
0x40107c __vbaFileOpen
0x401080 __vbaNew2
0x401084 None
0x401088 _adj_fdiv_m32i
0x40108c _adj_fdivr_m32i
0x401090 __vbaFreeStrList
0x401094 _adj_fdivr_m32
0x401098 _adj_fdiv_r
0x40109c None
0x4010a0 __vbaStrToAnsi
0x4010a4 _CIatan
0x4010a8 __vbaStrMove
0x4010ac _allmul
0x4010b0 _CItan
0x4010b4 _CIexp
0x4010b8 __vbaFreeObj
0x4010bc __vbaFreeStr
EAT(Export Address Table) is none