ScreenShot
| Created | 2024.10.16 11:26 | Machine | s1_win7_x6401 |
| Filename | Document.pdf.url | ||
| Type | MS Windows 95 Internet shortcut text (URL= |
||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | |||
| md5 | 4f26d833fbf311ce76485a8d7e15e078 | ||
| sha256 | 1c4964a53550d4e345f09c1935001ef874e009362167873ff563d035b5b6d066 | ||
| ssdeep | 3:J25YdimVVG/VClAWMtqRAbABGQEZagPWjtt5GRyn:J254vVG/4xtOFJQgPW7Zn | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (13cnts)
| Level | Description |
|---|---|
| watch | Communicates with host for which no DNS query was performed |
| watch | Connects to an IRC server |
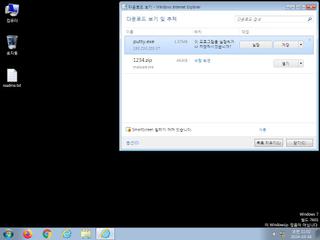
| watch | Putty Files |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | An application raised an exception which may be indicative of an exploit crash |
| notice | Creates executable files on the filesystem |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | URLs have been extracted from an Internet shortcut file |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
| info | One or more processes crashed |
Rules (15cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | IsPE64 | (no description) | binaries (download) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Suricata ids
ET INFO Executable Download from dotted-quad Host
ET HUNTING Possibly Suspicious Request for Putty.exe from Non-Standard Download Location
ET POLICY PE EXE or DLL Windows file download HTTP
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO TLS Handshake Failure
ET HUNTING Possibly Suspicious Request for Putty.exe from Non-Standard Download Location
ET POLICY PE EXE or DLL Windows file download HTTP
ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
ET INFO TLS Handshake Failure