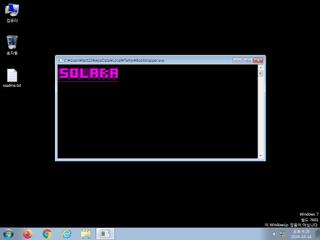
ScreenShot
| Created | 2024.10.16 21:29 | Machine | s1_win7_x6401 |
| Filename | Bootstrapper.exe | ||
| Type | PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows | ||
| AI Score |
|
Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | 58 detected (Common, Sdum, Artemis, MSILHeracles, Unsafe, Vpea, malicious, confidence, Attribute, HighConfidence, high confidence, AGen, MalwareX, CLOUD, iqkvn, AgentAGen, R002C0DJD24, Detected, Malware@#8wk1chln1w0o, Malgent, Eldorado, Chgt, Gencirc, jwIc7OWdAtA, Pstinb, susgen) | ||
| md5 | 2a4dcf20b82896be94eb538260c5fb93 | ||
| sha256 | ebbcb489171abfcfce56554dbaeacd22a15838391cbc7c756db02995129def5a | ||
| ssdeep | 12288:t0zVvgDNMoWjTmFzAzBocaKjyWtiR1pptHxQ0z:O5vgHWjTwAlocaKjyyItHDz | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 58 AntiVirus engines on VirusTotal as malicious |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a suspicious process |
| notice | Uses Windows utilities for basic Windows functionality |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | One or more processes crashed |
| info | Queries for the computername |
Rules (6cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (upload) |
| watch | Win32_Trojan_PWS_Net_1_Zero | Win32 Trojan PWS .NET Azorult | binaries (upload) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsPE64 | (no description) | binaries (upload) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)
PE API
IAT(Import Address Table) Library
mscoree.dll
0x4c94a8 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x4c94a8 _CorExeMain
EAT(Export Address Table) is none