ScreenShot
| Created | 2024.10.17 16:46 | Machine | s1_win7_x6403 |
| Filename | b.ps1 | ||
| Type | ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : mailcious | ||
| VT API (file) | |||
| md5 | 633e79b5e535ec56f58696658967b9d3 | ||
| sha256 | a8d577bf773f753dfb6b95a3ef307f8b4d9ae17bf86b95dcbb6b2fb638a629b9 | ||
| ssdeep | 48:XFgyp/3Zv8V4oq1AYzyLaUP+WuyaMS9QPSJrT27geRUGE5JY84hUoxalUV8GmFjI:KA3Zv8S1A2ZU2WuyaMYQPSpYbRqo8C | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
| danger | Connects to an IP address that is no longer responding to requests (legitimate services will remain up-and-running usually) |
| watch | Communicates with host for which no DNS query was performed |
| watch | Deletes executed files from disk |
| watch | One or more non-whitelisted processes were created |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks adapter addresses which can be used to detect virtual network interfaces |
| info | Checks amount of memory in system |
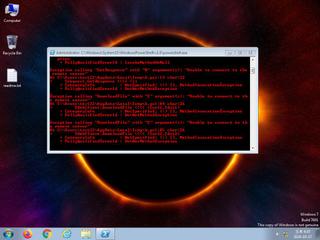
| info | Command line console output was observed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (2cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |